Jan 20, 2025Ravie Lakshmanan As the digital world becomes more complicated, the lines between national security and cybersecurity are starting […]
The latest Apple MacBook Air is down to its lowest price since Black Friday
(Image credit: Future) If your finances feel refreshed after the holidays, now is the time to check out the great […]
CrowdStrike outage prompts businesses to overhaul supply chains
The CrowdStrike outage of July 2024 has triggered a major rethink of tech supply chains, as businesses around the world […]
Product Walkthrough: How Satori Secures Sensitive Data From Production to AI
Every week seems to bring news of another data breach, and it’s no surprise why: securing sensitive data has become […]
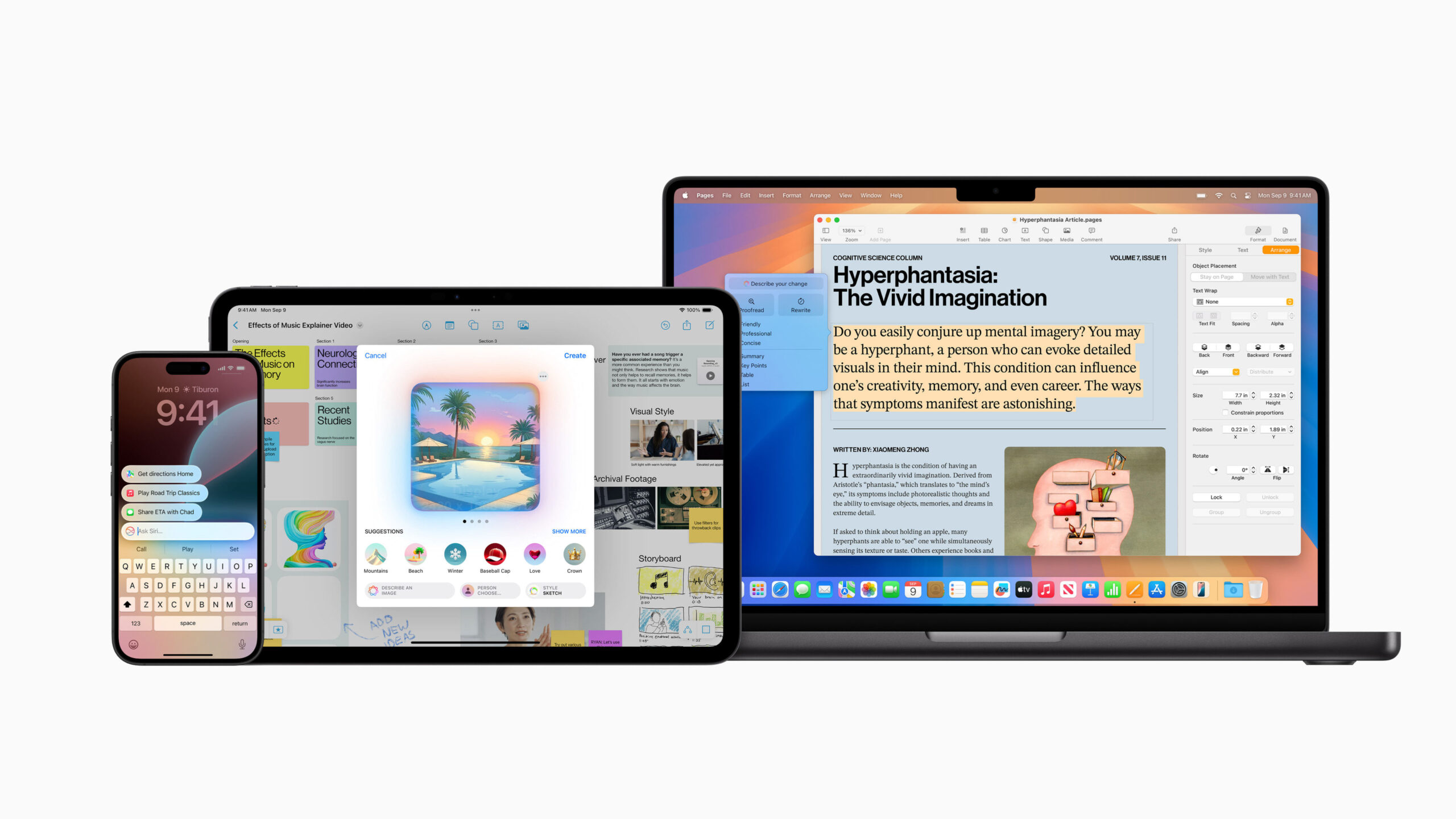
Huge Apple Intelligence upgrade expected for Mail as part of macOS Sequoia 15.4 free update
(Image credit: Apple) Mac users will get access to one of the most talked about Apple Intelligence features, Genmoji, in […]
The European Commission wants Elon Musk to reveal the secrets of the X recommendation algorithm (don’t we all?)
Elon Musk — or his company, X, at least — has been given until mid-February to provide the European Commission […]
Key developments and challenges in LLMs [Q&A]
Large language models (LLMs) have undergone rapid evolution in recent years, but can often be viewed as something of a […]
Windows 11 is finally getting a decent battery tool — here’s how to enable it so you know how much power you have left
Laptop users rejoice — Microsoft is finally getting around to making life a little easier for you. When you’re working […]
Hackers Deploy Malicious npm Packages to Steal Solana Wallet Keys via Gmail SMTP
Jan 20, 2025Ravie LakshmananSupply Chain Attack / Solana Cybersecurity researchers have identified three sets of malicious packages across the npm […]
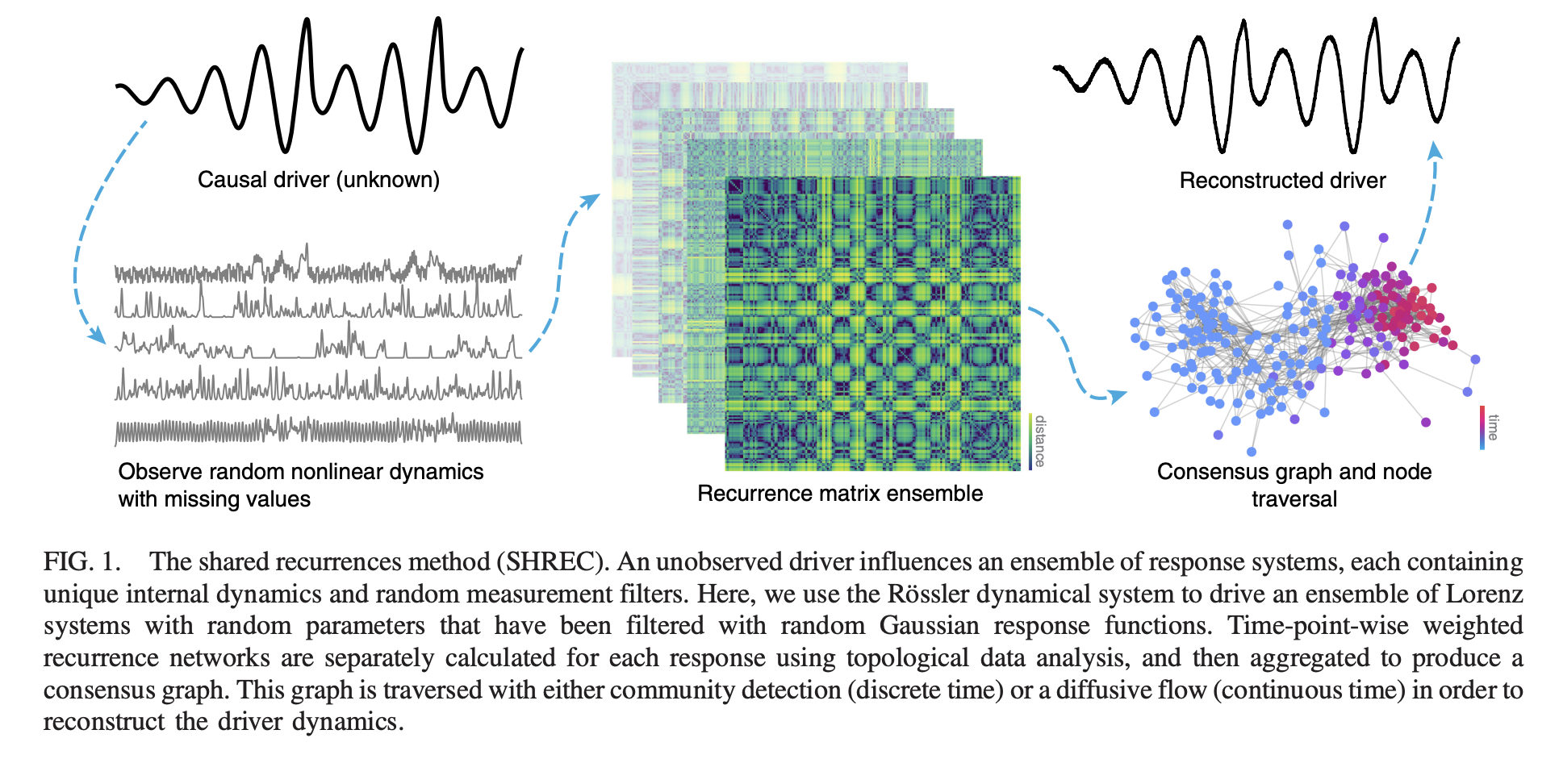
SHREC: A Physics-Based Machine Learning Approach to Time Series Analysis
Reconstructing unmeasured causal drivers of complex time series from observed response data represents a fundamental challenge across diverse scientific domains. […]



![⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips [20 January]](https://thetechbriefs.com/wp-content/uploads/2025/01/3116-thn-weekly-recap-top-cybersecurity-threats-tools-and-tips-20-january.png)


![Key developments and challenges in LLMs [Q&A]](https://thetechbriefs.com/wp-content/uploads/2025/01/3092-key-developments-and-challenges-in-llms-qa.jpg)