Dozens of cryptographically verified open source packages from Microsoft were compromised late last week to add advanced credential-stealing code that […]
Category: Biz & IT
How a USB-connected speaker can infect a PC without ever being touched
After successfully replacing the firmware with a replacement image that did nothing more than display the word “patched” on the […]
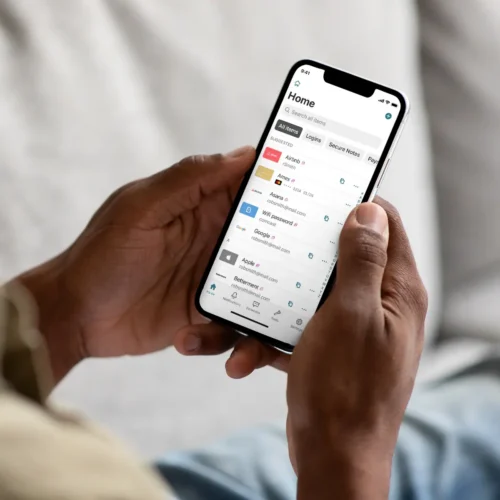
Dashlane explains how attackers managed to download encrypted password vaults
Skip to content By targeting large numbers of users, attackers increased their chances of success. Dashlane said that attackers mounted […]
Dashlane issues opaque advisory warning 20 encrypted vaults were stolen
There’s a lot that doesn’t add up in a security advisory password manager Dashlane published Monday, warning that attackers managed […]
Dozens of Red Hat packages backdoored through its official NPM channel
The worm, dubbed Shai-Hulud, has all the hallmarks of malware released last month as freely available open source. TeamPCP was […]
Botnet of more than 17 million devices dismantled
Authorities in the Netherlands said they dismantled a botnet that comprised more than 17 million devices and were managed by […]
Fed up with vibe coders, dev sneaks data-nuking prompt injection into their code
In response, Link updated the 1.10.0 release notes to disclose the verbatim prompt injection in its entirety. The section now […]
Websites have a new way to spy on visitors: analyzing their SSD activity
While each file system is sandboxed, meaning it’s isolated from other websites and from the device system itself, the JavaScript […]
Millions of AI agents imperiled by critical vulnerability in open source package
Millions of AI agents and tools around the world have been imperiled by a critical vulnerability that can allow hackers […]
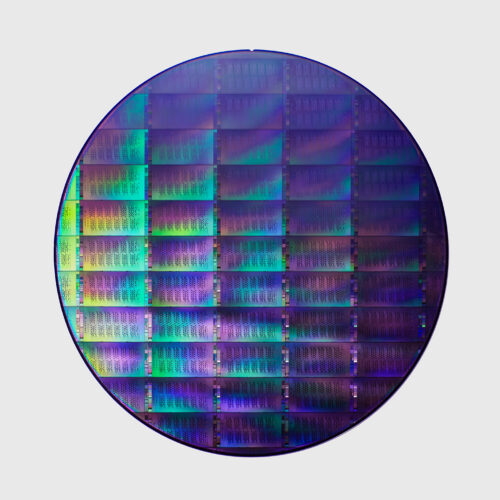
US’s big bet on quantum computing may not be entirely legal
Last week, the US government announced $2 billion in investments in quantum computing companies, allocating $100 million each to a […]