(Image credit: Future) It should come as no surprise to anyone familiar with my work that I spend quite a […]
Lazarus Group Targets Web3 Developers with Fake LinkedIn Profiles in Operation 99
Jan 15, 2025Ravie LakshmananCryptocurrency / Malware The North Korea-linked Lazarus Group has been attributed to a new cyber attack campaign […]
Security and compliance are biggest barriers to cloud adoption
Cloud adoption is at the heart of digital transformation, providing organizations with the agility and flexibility they need to stay […]
Microsoft’s Copilot+ PC price cuts didn’t help disappointing sales apparently – but there’s still a glimmer of hope
(Image credit: Future / John Loeffler) Analyst firm Context has shared sales data for Q4 2024 Copilot+ PCs didn’t see […]
This Asus TUF gaming laptop with an RTX 4070 is down to its lowest-ever price
(Image credit: Future) The latest Nvidia GeForce 50-series of graphics cards were unveiled earlier this month and that’s led to […]
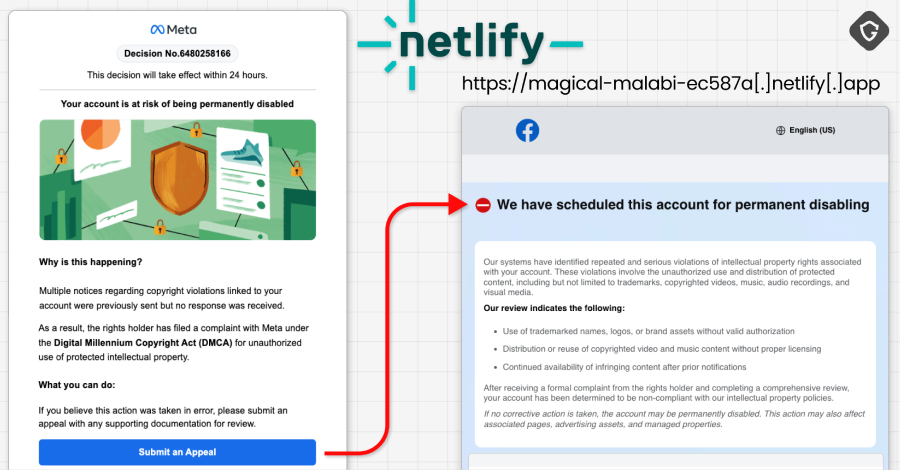
68 percent of organizations don’t fix critical vulnerabilities on time
A newly-released report from Swimlane shows that a worrying 68 percent of organizations say remediating a critical vulnerability takes them […]
I can’t believe I’m saying this, but Nvidia, good on you – RTX 4000 series GPUs will receive DLSS Frame Generation enhancements this month
(Image credit: Nvidia) Nvidia will bring Frame Generation enhancements to the RTX 4000 series DLSS 4 will be accessible to […]
New LLM-powered engine helps secure complex cloud environments
While moving systems to the cloud delivers many benefits, it also leads to complex dynamic environments that can be a […]
North Korean IT Worker Fraud Linked to 2016 Crowdfunding Scam and Fake Domains
Jan 15, 2025Ravie LakshmananBlockchain / Cryptocurrency Cybersecurity researchers have identified infrastructure links between the North Korean threat actors behind the […]
Google Cloud Researchers Uncover Flaws in Rsync File Synchronization Tool
Jan 15, 2025Ravie LakshmananVulnerability / Software Update As many as six security vulnerabilities have been disclosed in the popular Rsync […]