Dec 10, 2024The Hacker NewsMalware Analysis / Cyber Threat Cyber attackers never stop inventing new ways to compromise their targets. […]
Don’t buy a router, buy a fast and secure ASUS WiFi 7 extendable router
(Image credit: Asus) Now that there’s a larger selection of WiFi 7 devices from mainstream mobile phones such as iPhone […]
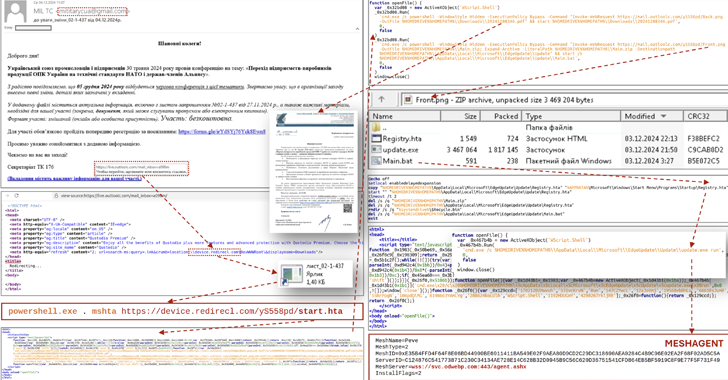
CERT-UA Warns of Phishing Attacks Targeting Ukraine’s Defense and Security Force
Dec 10, 2024Ravie LakshmananMalware / Cyber Attack The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new […]
How AI is Enhancing Cloud Performance and Cost Optimization?
Artificial Intelligence (AI) transforms cloud infrastructures, bringing unprecedented efficiency, scalability, and performance. As businesses increasingly adopt cloud environments to manage […]
Quordle today – hints and answers for Tuesday, December 10 (game #1051)
(Image credit: Getty Images) Quordle was one of the original Wordle alternatives and is still going strong now more than […]
NYT Strands today — hints, answers and spangram for Tuesday, December 10 (game #282)
Strands is the NYT’s latest word game after the likes of Wordle, Spelling Bee and Connections – and it’s great […]
Black Basta Ransomware Evolves with Email Bombing, QR Codes, and Social Engineering
Dec 09, 2024Ravie LakshmananThreat Intelligence / Malware The threat actors linked to the Black Basta ransomware have been observed switching […]
⚡ THN Recap: Top Cybersecurity Threats, Tools and Tips (Dec 2 – 8)
Dec 09, 2024Ravie LakshmananCyber Threats / Weekly Recap This week’s cyber world is like a big spy movie. Hackers are […]
Researchers Uncover Prompt Injection Vulnerabilities in DeepSeek and Claude AI
Dec 09, 2024Ravie LakshmananArtificial Intelligenc / Vulnerability Details have emerged about a now-patched security flaw in the DeepSeek artificial intelligence […]
Seven Bolt-Ons to Make Your Entra ID More Secure for Critical Sessions
Identity security is all the rage right now, and rightfully so. Securing identities that access an organization’s resources is a […]