(Image credit: Shutterstock / LookerStudio) Natural language refers to the regular speech and text that we use to communicate with […]
Orico O7000 SSD review: high-end PCIe 4.0 storage without the frills
TechRadar Verdict Orico’s O7000 1TB is a great drive for anyone operating on a budget thanks to its great performance […]
New HIPAA Rules Mandate 72-Hour Data Restoration and Annual Compliance Audits
Dec 30, 2025Ravie LakshmananCybersecurity / Compliance The United States Department of Health and Human Services’ (HHS) Office for Civil Rights […]
You can love or hate AI, but it’s killed crappy 8GB versions of pricey PCs and Macs
Skip to content Op-ed: AI has been a cure for $1,600 computers that start with 8GB of memory. I’d describe […]
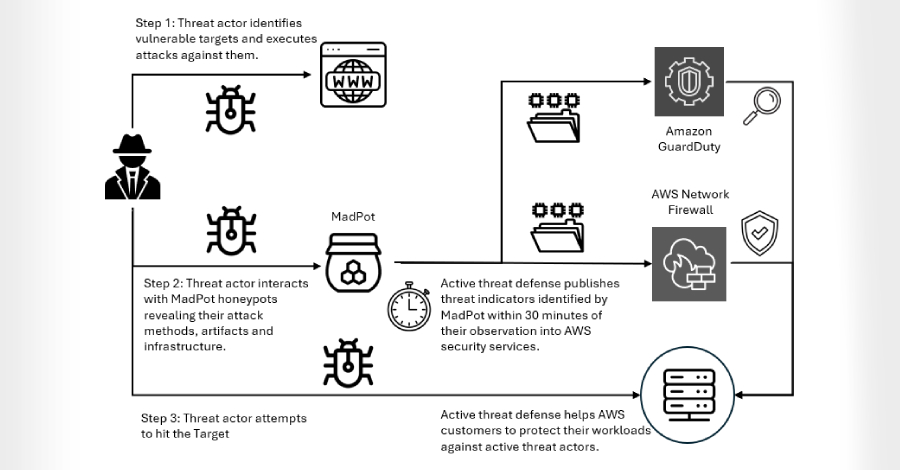
⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips
Dec 30, 2025Ravie LakshmananCybersecurity / Hacking News Every week, the digital world faces new challenges and changes. Hackers are always […]
Passkey technology is elegant, but it’s most definitely not usable security
NOT (QUITE) READY FOR PRIMETIME Just in time for holiday tech-support sessions, here’s what to know about passkeys. It’s that […]
When Good Extensions Go Bad: Takeaways from the Campaign Targeting Browser Extensions
Dec 30, 2025The Hacker NewsBrowser Security / GenAI Security News has been making headlines over the weekend of the extensive […]
Microsoft in 2024: year in review
(Image credit: Future / John Loeffler) Microsoft ushered in what the company billed as the future of computing this year, […]
Understanding and taking control of your data ecosystem [Q&A]
Data comes in many forms, it may be structured, it may be unstructured, it could be sensitive or purely statistical. […]
Handheld gaming PCs are here to stay: here’s why I’d recommend the Asus ROG Ally over a gaming laptop any day of the week
(Image credit: Asus) I’ve been a PC gamer for basically my entire life. Even as a young kid on my […]













![Understanding and taking control of your data ecosystem [Q&A]](https://thetechbriefs.com/wp-content/uploads/2024/12/1438-understanding-and-taking-control-of-your-data-ecosystem-qa.jpg)