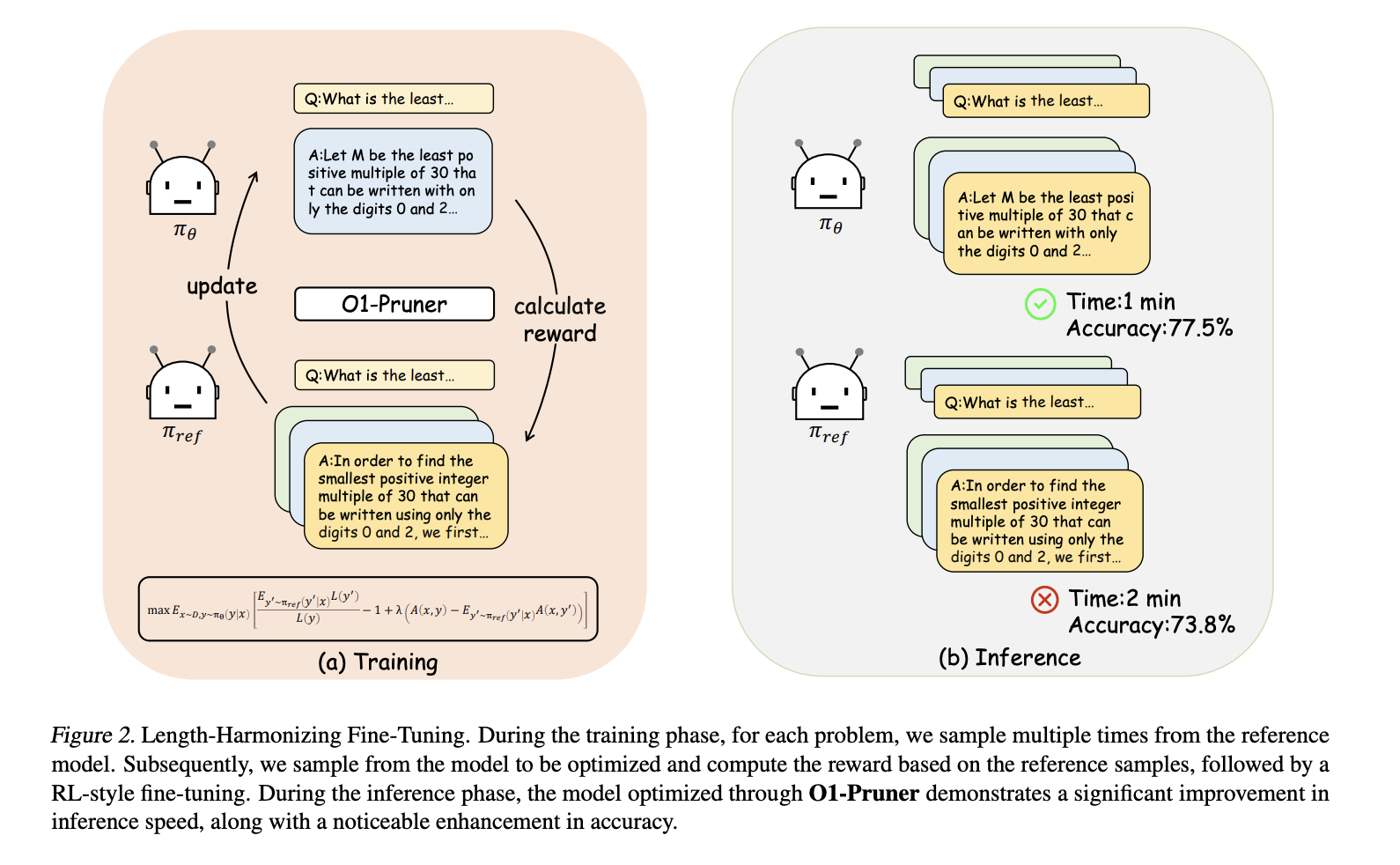
Large language models (LLMs) have introduced impressive capabilities, particularly in reasoning tasks. Models like OpenAI’s O1 utilize “long-thought reasoning,” where […]
CISA Adds Five-Year-Old jQuery XSS Flaw to Exploited Vulnerabilities List
Jan 24, 2025Ravie LakshmananVulnerability / JavaScript The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday placed a now-patched security […]
Configure a Linux Firewall: Three Approaches
A Linux firewall is crucial for safeguarding your system against unauthorized access and cyber threats. By setting up specific firewall […]
Are these AI-designed shoes the future of footwear?
(Image credit: Syntilay) Syntilay has launched AI-designed, 3D-printed shoes. The footwear was designed with a mix of Midjourney and Vizcom […]
Mobile-Agent-E: A Hierarchical Multi-Agent Framework Combining Cognitive Science and AI to Redefine Complex Task Handling on Smartphones
Smartphones are essential tools in dAIly life. However, the complexity of tasks on mobile devices often leads to frustration and […]
Google AI Introduces Learn-by-Interact: A Data-Centric Framework for Adaptive and Efficient LLM Agent Development
The study of autonomous agents powered by large language models (LLMs) has shown great promise in enhancing human productivity. These […]
Vivaldi 7.1 brings privacy-focused features to Windows, Mac, and Linux
Vivaldi has made version 7.1 of its web browser available for download here. This version introduces many powerful new features […]
Perplexity’s AI assistant goes mobile on Android
(Image credit: Perplexity) Perplexity AI has released a mobile app for Android The Perplexity Assistant offers voice, text, and camera-based […]
Quordle today – my hints and answers for Friday, January 24 (game #1096)
(Image credit: Getty Images) Quordle was one of the original Wordle alternatives and is still going strong now more than […]
Backdoor infecting VPNs used “magic packets” for stealth and security
When threat actors use backdoor malware to gain access to a network, they want to make sure all their hard […]