(Image credit: Getty Images) Quordle was one of the original Wordle alternatives and is still going strong now more than […]
NYT Strands today — hints, answers and spangram for Monday, December 9 (game #281)
Strands is the NYT’s latest word game after the likes of Wordle, Spelling Bee and Connections – and it’s great […]
NYT Strands today — hints, answers and spangram for Sunday, December 8 (game #280)
(Image credit: New York Times) Strands is the NYT’s latest word game after the likes of Wordle, Spelling Bee and […]
Quordle today – hints and answers for Sunday, December 8 (game #1049)
(Image credit: Getty Images) Quordle was one of the original Wordle alternatives and is still going strong now more than […]
This math app could make you your child’s teaching hero
(Image credit: Future) I wonder what math classes were like for you when you were young. With no desire to […]
Learn How Experts Secure Privileged Accounts—Proven PAS Strategies Webinar
Dec 07, 2024The Hacker NewsEnterprise Security / Threat Prevention Cybercriminals know that privileged accounts are the keys to your kingdom. […]
Ultralytics AI Library Compromised: Cryptocurrency Miner Found in PyPI Versions
Dec 07, 2024Ravie LakshmananSupply Chain Attack / Cryptocurrency In yet another software supply chain attack, it has come to light […]
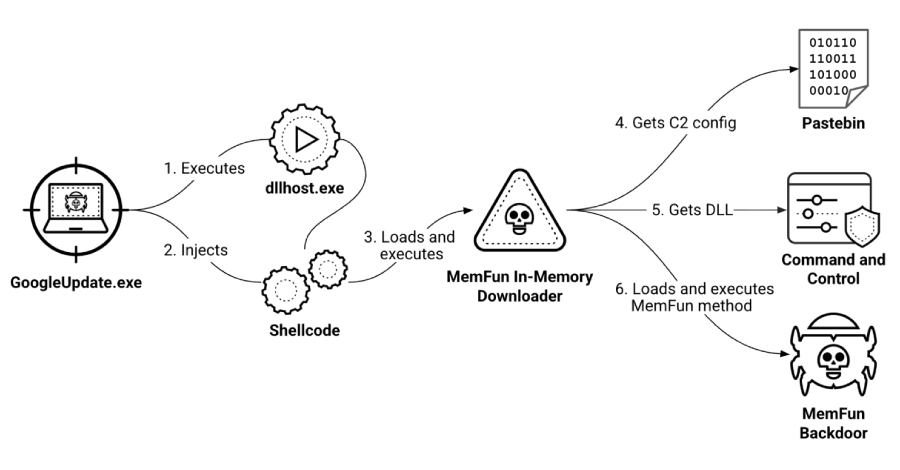
Hackers Using Fake Video Conferencing Apps to Steal Web3 Professionals’ Data
Dec 07, 2024Ravie LakshmananMalware / Web3 Security Cybersecurity researchers have warned of a new scam campaign that leverages fake video […]
Romania Cancels Presidential Election Results After Alleged Russian Meddling on TikTok
Dec 07, 2024Ravie LakshmananCybersecurity / Election Fraud In a historic decision, Romania’s constitutional court has annulled the result of the […]
The Rise of AI-Augmented Professions: How AI is Enhancing Human Expertise
In recent years, the rapid advancement of artificial intelligence (AI) has sparked both excitement and concern across various industries. While […]