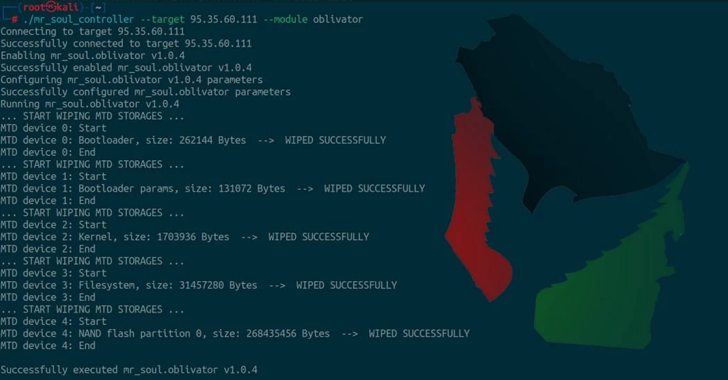
Dec 13, 2024The Hacker NewsIoT Security / Operational Technology Iran-affiliated threat actors have been linked to a new custom malware […]
Windows 11’s ‘suggested actions’ feature is headed to the Microsoft Graveyard – but here’s what’s replacing it
Microsoft is deprecating Windows 11’s “Suggested Actions” menu, introduced in 2022 A new AI-powered tool, “Click to Do,” will replace […]
How to Generate a CrowdStrike RFM Report With AI in Tines
Run by the team at orchestration, AI, and automation platform Tines, the Tines library contains pre-built workflows shared by real […]
Nvidia cranks RTX 5000 GPU hype machine up to full speed, teasing ‘GeForce at CES 2025’ as Witcher 4 trailer drops a big hint
(Image credit: Gigabyte) Nvidia has teased revelations about ‘GeForce at CES 2025’ This must surely be next-gen GPUs, likely the […]
Keynote, Pages, and Numbers just got way better with this free Apple Intelligence update – here’s how
Apple’s iWork suite is available for iOS/iPadOS devices and macOS. (Image credit: Apple) Apple has updated its iWork suite of […]
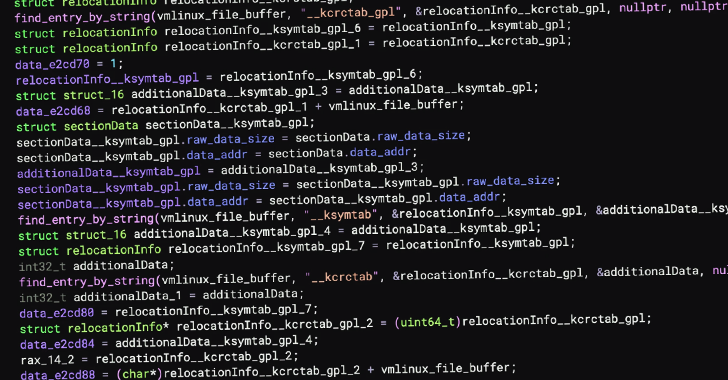
New Linux Rootkit PUMAKIT Uses Advanced Stealth Techniques to Evade Detection
Dec 13, 2024Ravie LakshmananLinux / Threat Analysis Cybersecurity researchers have uncovered a new Linux rootkit called PUMAKIT that comes with […]
FBI Busts Rydox Marketplace with 7,600 PII Sales, Cryptocurrency Worth $225K Seized
The U.S. Department of Justice (DoJ) on Thursday announced the shutdown of an illicit marketplace called Rydox (“rydox[.]ru” and “rydox[.]cc”) […]
Building Secure Web Applications: A Conceptual Approach to Front-End Development and Cybersecurity
Cybersecurity has become critical to web application security, particularly through robust front-end development practices. This article offers a conceptual framework […]
High-speed NBN plans have never been this cheap – or fast
(Image credit: Future / Getty) Our reliance on a fast, stable internet connection has never been more important. It’s estimated […]
NYT Strands today — my hints, answers and spangram for Friday, December 13 (game #285)
Strands is the NYT’s latest word game after the likes of Wordle, Spelling Bee and Connections – and it’s great […]