Drug sales on the dark web are trending downward in favor of Snapchat, Telegram, and others. For every illegal drug, […]
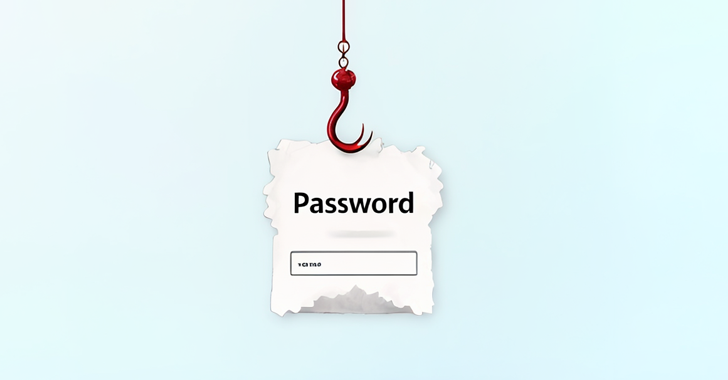
Threat actors spoof email security providers
A new report from phishing defense company Cofense highlights increasingly sophisticated phishing attacks that are exploiting trusted email security companies […]
Get ‘The Data Science Handbook, 2nd Edition’ for FREE and save $60!
Becoming a data scientist is hard. The job focuses on mathematical tools, but also demands fluency with software engineering, understanding […]
HubPhish Exploits HubSpot Tools to Target 20,000 European Users for Credential Theft
Dec 18, 2024Ravie LakshmananEmail Security / Cloud Security Cybersecurity researchers have disclosed a new phishing campaign that has targeted European […]
Credential phishing attacks up over 700 percent
Phishing remains one of the most significant cyber threats impacting organizations worldwide and a new report shows credential theft attacks […]
What will attackers target in 2025? CNI, CNI, and more CNI!
Critical national infrastructure (CNI) has had a rough 2024 in the UK when it comes to cybercrime. From the chaos […]
Russian space chief says country will fly on space station until 2030
“Space is an area of activity where there is never a 100 percent guaranteed result, and failures hound everyone,” he […]
It looks like macOS Sequoia 15.2 update breaks third-party bootable backups – and that has me worried
(Image credit: Shutterstock/fizkes) macOS Sequoia 15.2 impacts third-party apps, complicating full-drive backups and bootable recovery options Apple pushes Time Machine, […]
Huawei has surprised us with one of the best laptop deals you can buy right now
(Image credit: Future) Laptops are designed to be used at home, while out and about, and in the office. To […]
How to use ChatGPT’s new Projects feature to bring order to OpenAI’s chatbot
(Image credit: Shutterstock / Primakov) ChatGPT’s new Projects feature is a life preserver to those who enjoy ChatGPT but are […]