Skip to content OK, but what about Winds of Winter? “I couldn’t help but wonder if a simple underlying model […]
MSI introduces Strike 600 mechanical keyboard designed for quiet performance
MSI has announced the Strike 600, a mechanical keyboard aimed at providing a quieter typing and gaming experience while offering […]
Nvidia RTX 5090 8K performance has blown me away already – and it’s mainly thanks to Multi-Frame Generation
(Image credit: Nvidia / Future) Our 8K test system PC built by Stormforce Gaming Motherboard: Asus PRIME Z-790P LGA 1700Processor: […]
Palo Alto Firewalls Found Vulnerable to Secure Boot Bypass and Firmware Exploits
Jan 23, 2025Ravie LakshmananFirmware Security / Vulnerability An exhaustive evaluation of three firewall models from Palo Alto Networks has uncovered […]
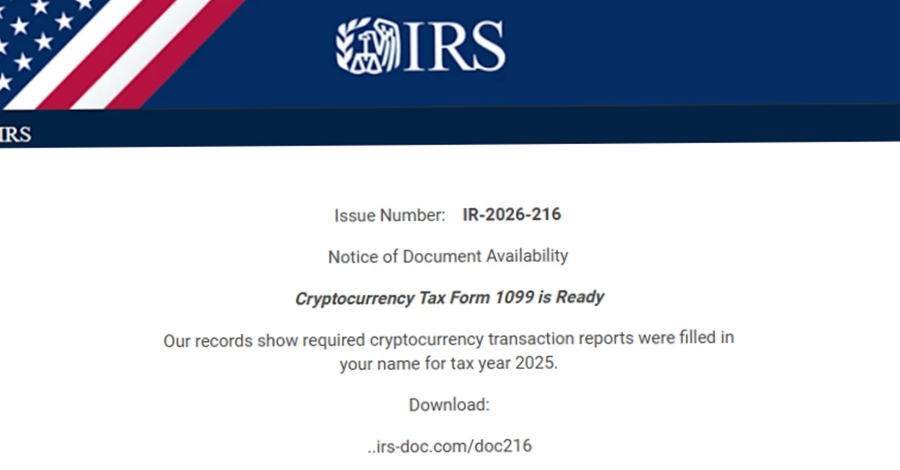
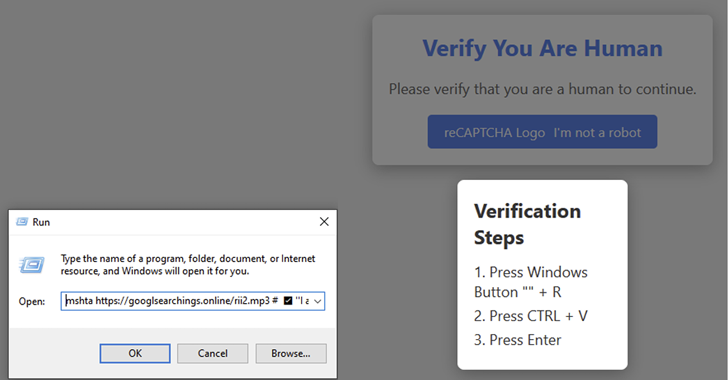
Beware: Fake CAPTCHA Campaign Spreads Lumma Stealer in Multi-Industry Attacks
Jan 23, 2025Ravie LakshmananPhishing / Malware Cybersecurity researchers are calling attention to a new malware campaign that leverages fake CAPTCHA […]
Custom Backdoor Exploiting Magic Packet Vulnerability in Juniper Routers
Jan 23, 2025Ravie LakshmananMalware / Enterprise Security Enterprise-grade Juniper Networks routers have become the target of a custom backdoor as […]
UK opens probe into Google’s and Apple’s mobile platforms
Last week, the CMA opened its first such case, reviewing Google’s dominance in search and advertising. The CMA is already […]
CISOs get more time in the boardroom but struggle with budgets
A new report from Splunk shows 82 percent of CISOs now report directly to the CEO, up from 47 percent […]
Trust me, 2025’s lineup of gaming handhelds may be the best yet with Aokzoe’s A1 X taking the fight to the Nintendo Switch 2 and Asus ROG Ally X
(Image credit: Siberian Art / Shutterstock) Aokzoe is ready to compete with other gaming handhelds this year with the A1 […]
Experts Find Shared Codebase Linking Morpheus and HellCat Ransomware Payloads
Jan 23, 2025Ravie LakshmananThreat Intelligence / Data Breach An analysis of HellCat and Morpheus ransomware operations has revealed that affiliates […]