Ravie LakshmananApr 24, 2026Malware / Threat Intelligence Chinese-speaking individuals are the target of a new campaign that uses a trojanized […]
Category: Security
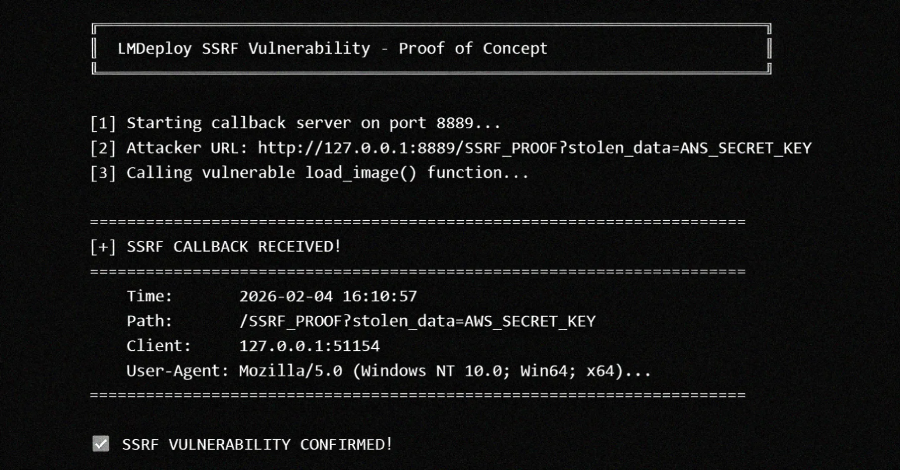
LMDeploy CVE-2026-33626 Flaw Exploited Within 13 Hours of Disclosure
A high-severity security flaw in LMDeploy, an open-source toolkit for compressing, deploying, and serving LLMs, has come under active exploitation […]
In a first, a ransomware family is confirmed to be quantum-safe
There is no practical benefit for Kyber developers to have chosen a PQC key-exchange algorithm. The Kyber ransom note gives […]
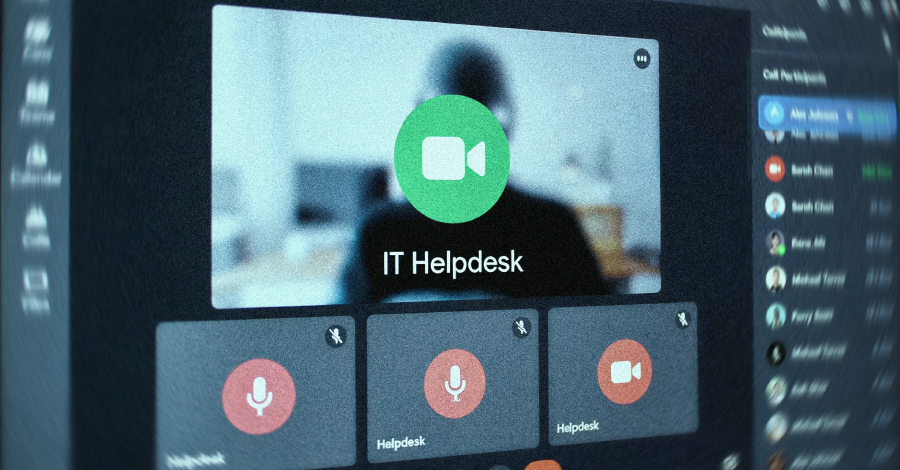
‘Identity is the new battleground’: Why your IT helpdesk is suddenly getting a lot of bizarre calls
Attackers now call helpdesks instead of sending phishing emails to breach networks Impostors pose as executives to manipulate support teams […]
UNC6692 Impersonates IT Helpdesk via Microsoft Teams to Deploy SNOW Malware
A previously undocumented threat activity cluster known as UNC6692 has been observed leveraging social engineering tactics via Microsoft Teams to […]
Bitwarden CLI Compromised in Ongoing Checkmarx Supply Chain Campaign
Bitwarden CLI has been compromised as part of the newly discovered and ongoing Checkmarx supply chain campaign, according to new […]
ThreatsDay Bulletin: $290M DeFi Hack, macOS LotL Abuse, ProxySmart SIM Farms +25 New Stories
You scroll past one incident and see another that feels familiar, like it should have been fixed years ago, but […]
[Webinar] Mythos Reality Check: Beating Automated Exploitation at AI Speed
The Hacker NewsApr 23, 2026Artificial Intelligence / Enterprise Security Imagine a world where hackers don’t sleep, don’t take breaks, and […]
Project Glasswing Proved AI Can Find the Bugs. Who’s Going to Fix Them?
Last week, Anthropic announced Project Glasswing, an AI model so effective at discovering software vulnerabilities that they took the extraordinary […]
China-Linked GopherWhisper Infects 12 Mongolian Government Systems with Go Backdoors
Ravie LakshmananApr 23, 2026Threat Intelligence / Malware Mongolian governmental institutions have emerged as the target of a previously undocumented China-aligned […]





![[Webinar] Mythos Reality Check: Beating Automated Exploitation at AI Speed](https://thetechbriefs.com/wp-content/uploads/2026/04/139729-webinar-mythos-reality-check-beating-automated-exploitation-at-ai-speed.jpg)