A pro-Ukrainian hacktivist group called PhantomCore has been attributed to attacks actively targeting servers running TrueConf video conferencing software in […]
Category: Security
Researchers Uncover 73 Fake VS Code Extensions Delivering GlassWorm v2 Malware
Ravie LakshmananApr 27, 2026Malware / Software Supply Chain Cybersecurity researchers have flagged dozens of Microsoft Visual Studio Code (VS Code) […]
Fake CAPTCHA IRSF Scam and 120 Keitaro Campaigns Drive Global SMS, Crypto Fraud
Cybersecurity researchers have disclosed details of a telecommunications fraud campaign that uses fake CAPTCHA verification tricks to dupe unsuspecting users […]
Researchers Uncover Pre-Stuxnet ‘fast16’ Malware Targeting Engineering Software
Cybersecurity researchers have discovered a new Lua-based malware created years before the notorious Stuxnet worm that aimed to sabotage Iran’s […]
CISA Adds 4 Exploited Flaws to KEV, Sets May 2026 Federal Deadline
Ravie LakshmananApr 25, 2026Network Security / Infrastructure Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added four […]
Why are top university websites serving porn? It comes down to shoddy housekeeping.
With that, they have now hijacked that university’s subdomain. Given the reputations universities have, search queries then flow to the […]
FIRESTARTER Backdoor Hit Federal Cisco Firepower Device, Survives Security Patches
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has revealed that an unnamed federal civilian agency’s Cisco Firepower device running […]
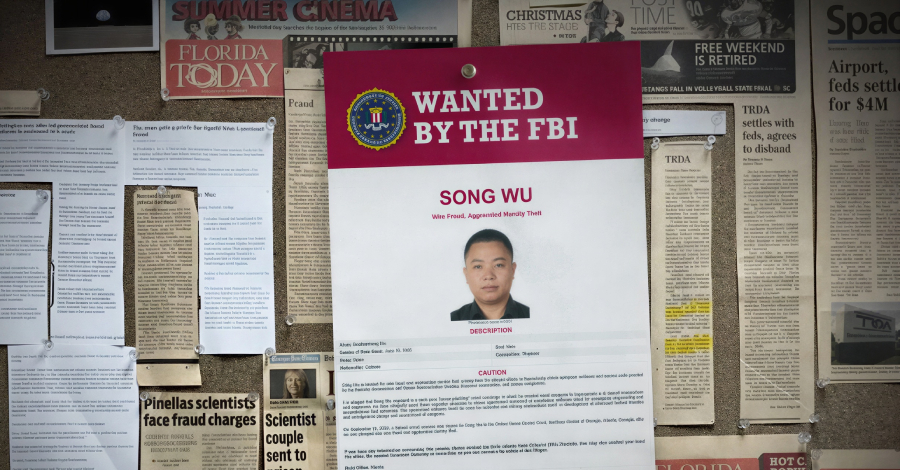
NASA Employees Duped in Chinese Phishing Scheme Targeting U.S. Defense Software
Ravie LakshmananApr 24, 2026Espionage / National Security, The Office of Inspector General (OIG) of the U.S. National Aeronautics and Space […]
Bridging the AI Agent Authority Gap: Continuous Observability as the Decision Engine
The AI Agent Authority Gap – From Ungoverned to Delegation As discussed in our previous article, AI agents are exposing […]
26 FakeWallet Apps Found on Apple App Store Targeting Crypto Seed Phrases
Cybersecurity researchers have discovered a set of malicious apps on the Apple App Store that impersonate popular cryptocurrency wallets in […]