Jan 17, 2025Ravie LakshmananWeb Security / Botnet Cybersecurity researchers have exposed a new campaign that targets web servers running PHP-based […]
Category: Security
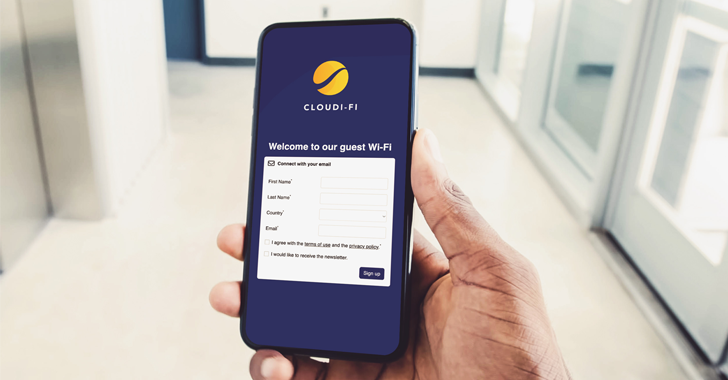
How to Bring Zero Trust to Wi-Fi Security with a Cloud-based Captive Portal?
Recent data breaches have highlighted the critical need to improve guest Wi-Fi infrastructure security in modern business environments. Organizations face […]
U.S. Sanctions North Korean IT Worker Network Supporting WMD Programs
Jan 17, 2025Ravie LakshmananInsider Threat / Cryptocurrency The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) sanctioned two individuals […]
New ‘Sneaky 2FA’ Phishing Kit Targets Microsoft 365 Accounts with 2FA Code Bypass
Jan 17, 2025Ravie LakshmananCybersecurity / Threat Intelligence Cybersecurity researchers have detailed a new adversary-in-the-middle (AitM) phishing kit that’s capable of […]
European Privacy Group Sues TikTok and AliExpress for Illicit Data Transfers to China
Austrian privacy non-profit None of Your Business (noyb) has filed complaints accusing companies like TikTok, AliExpress, SHEIN, Temu, WeChat, and […]
Russian Star Blizzard Shifts Tactics to Exploit WhatsApp QR Codes for Credential Harvesting
Jan 16, 2025Ravie LakshmananSpear Phishing / Threat Intelligence The Russian threat actor known as Star Blizzard has been linked to […]
Data privacy in 2025: The resurgence of biometric security, a fleeting forecast for federal data privacy regulations, and the return of the wild west of AI
The transition from 2024 to 2025 brings a lot of uncertainty, speculation, and hopefully some optimism for the world of […]
Microsoft patches Windows to eliminate Secure Boot bypass threat
For the past seven months—and likely longer—an industry-wide standard that protects Windows devices from firmware infections could be bypassed using […]
Ready to Simplify Trust Management? Join Free Webinar to See DigiCert ONE in Action
Jan 16, 2025The Hacker NewsCertificate Management / Compliance The digital world is exploding. IoT devices are multiplying like rabbits, certificates […]
The $10 Cyber Threat Responsible for the Biggest Breaches of 2024
You can tell the story of the current state of stolen credential-based attacks in three numbers: Stolen credentials were the […]