Ravie LakshmananMay 12, 2026Encryption / Mobile Security
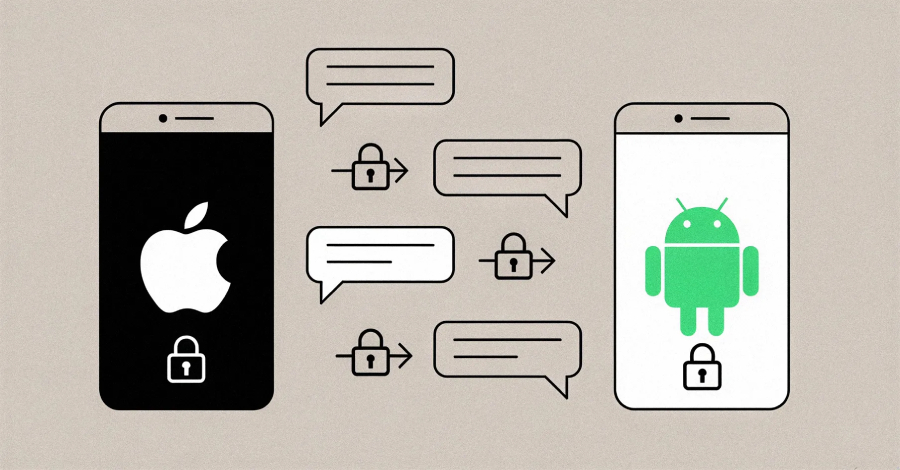
Apple on Monday officially released iOS 26.5 with support for end-to-end encryption (E2EE) to Rich Communication Services (RCS) in beta as part of a “cross-industry effort” to replace traditional SMS with a more secure alternative.
To that end, E2EE RCS messaging is rolling out to iPhone users running iOS 26.5 with supported carriers and Android users on the latest version of Google Messages. The feature is enabled by default for both new and existing conversations in both platforms.
RCS is a modern, internet-based messaging protocol that allows Android and iPhone users to send high-resolution photos and videos, see typing indicators, and receive read receipts, features all typically present in instant messaging apps. It is built on an industry specification called the RCS Universal Profile.
“When RCS messages are end-to-end encrypted, they can’t be read while they’re sent between devices,” Apple said in a statement. “Users will know that a conversation is end-to-end encrypted when they see a new lock icon in their RCS chats.”
Apple began testing with E2EE in RCS messages in iOS and iPadOS 26.4 Beta, initially limiting it to only conversations between Apple devices. In early 2025, the GSM Association (GSMA) announced support for E2EE for safeguarding messages sent via the RCS protocol.
In a similar statement, Google said Google Messages for Android users will see a padlock icon to indicate that the cross-platform conversation is end-to-end encrypted.
“This welcome progress is the result of close, cross‑industry collaboration between the GSMA RCS Working Group, including Apple, Google, and the wider mobile ecosystem,” Alex Sinclair, chief technology officer at GSMA, said. “Crucially, the new secure services are being delivered on an open, globally recognised foundation.”
The latest updates also come with fixes for over 50 vulnerabilities in iOS and iPadOS, including various flaws in AppleJPEG, ImageIO, Kernel, mDNSResponder, and WebKit that could be exploited to leak sensitive information, a denial-of-service (DoS), or result in unexpected system termination.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.