Ravie LakshmananMay 01, 2026Supply Chain Attack / Malware A new software supply chain attack campaign has been observed using sleeper […]
Category: Security
The most severe Linux threat to surface in years catches the world flat-footed
Publicly released exploit code for an effectively unpatched vulnerability that gives root access to virtually all releases of Linux is […]
PyTorch Lightning and Intercom-client Hit in Supply Chain Attacks to Steal Credentials
Ravie LakshmananApr 30, 2026Supply Chain Attack / Malware In yet another software supply chain attack, threat actors have managed to […]
ThreatsDay Bulletin: SMS Blaster Busts, OpenEMR Flaws, 600K Roblox Hacks and 25 More Stories
The internet is noisy this week. We are seeing some wild new tactics, like people using fake cell towers to […]
New Python Backdoor Uses Tunneling Service to Steal Browser and Cloud Credentials
Ravie LakshmananApr 30, 2026Cloud Security / Threat Intelligence Cybersecurity researchers have disclosed details of a stealthy Python-based backdoor framework called […]
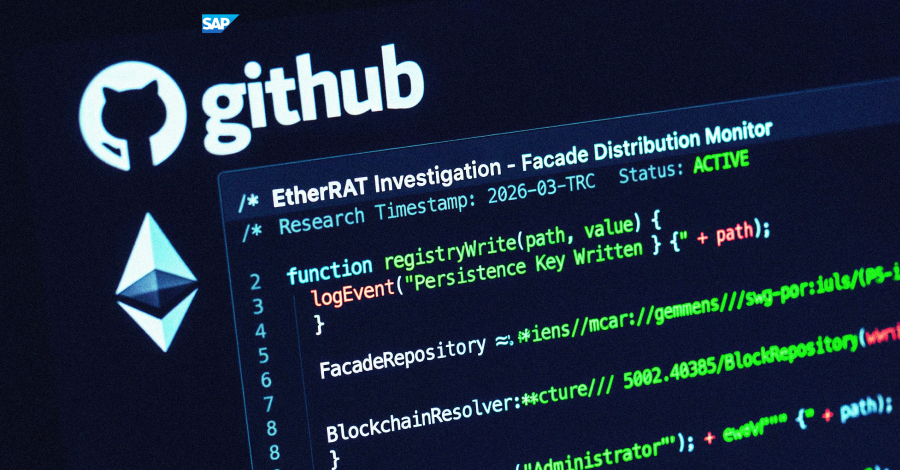
EtherRAT Distribution Spoofing Administrative Tools via GitHub Facades
Intro A sophisticated, high-resilience malicious campaign was identified by Atos Threat Research Center (TRC) in March 2026. This operation specifically […]
New Linux ‘Copy Fail’ Vulnerability Enables Root Access on Major Distributions
Ravie LakshmananApr 30, 2026Linux / Vulnerability Cybersecurity researchers have disclosed details of a Linux local privilege escalation (LPE) flaw that […]
Google Fixes CVSS 10 Gemini CLI CI RCE and Cursor Flaws Enable Code Execution
Google has addressed a maximum severity security flaw in Gemini CLI — the “@google/gemini-cli” npm package and the “google-github-actions/run-gemini-cli” GitHub […]
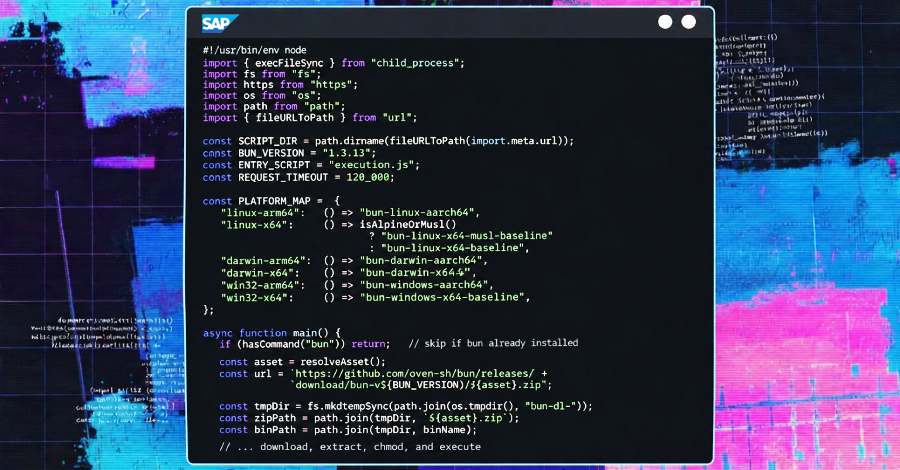
SAP-Related npm Packages Compromised in Credential-Stealing Supply Chain Attack
Ravie LakshmananApr 29, 2026Supply Chain Attack / Malware Cybersecurity researchers are sounding the alarm about a new supply chain attack […]
New Wave of DPRK Attacks Uses AI-Inserted npm Malware, Fake Firms, and RATs
Cybersecurity researchers have discovered malicious code in an npm package after a malicious package as a dependency to the project […]