There will now be a new version of Google Chrome every two weeks following the announcement of a dramatic acceleration […]
Category: Security
APT41-Linked Silver Dragon Targets Governments Using Cobalt Strike and Google Drive C2
Ravie LakshmananMar 04, 2026Malware / Windows Security Cybersecurity researchers have disclosed details of an advanced persistent threat (APT) group dubbed […]
CISA Adds Actively Exploited VMware Aria Operations Flaw CVE-2026-22719 to KEV Catalog
Ravie LakshmananMar 04, 2026Vulnerability / Enterprise Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a recently […]
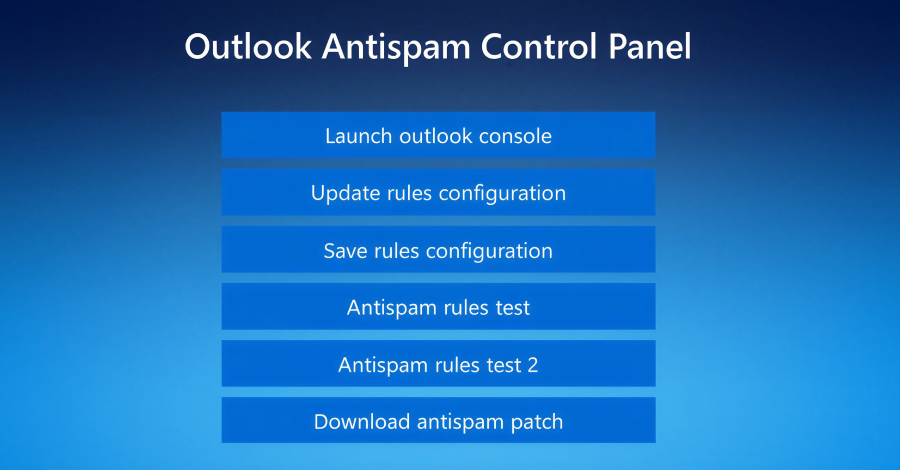
Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support […]
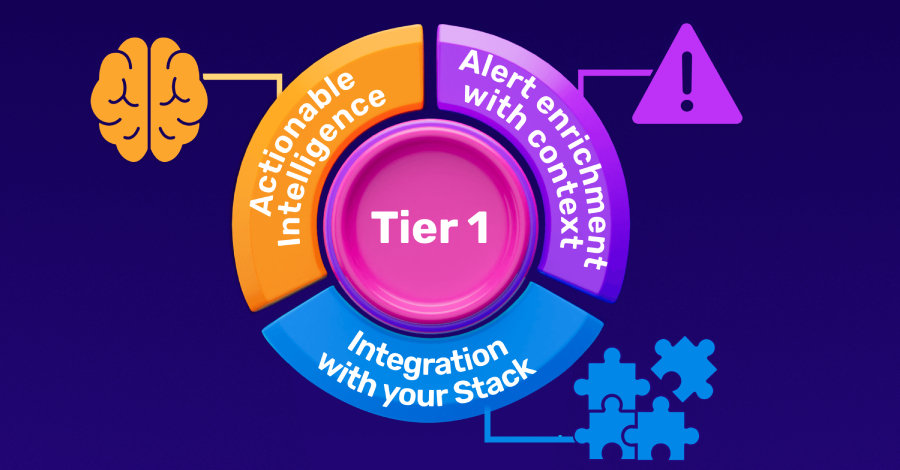
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
Every CISO knows the uncomfortable truth about their Security Operations Center: the people most responsible for catching threats in real […]
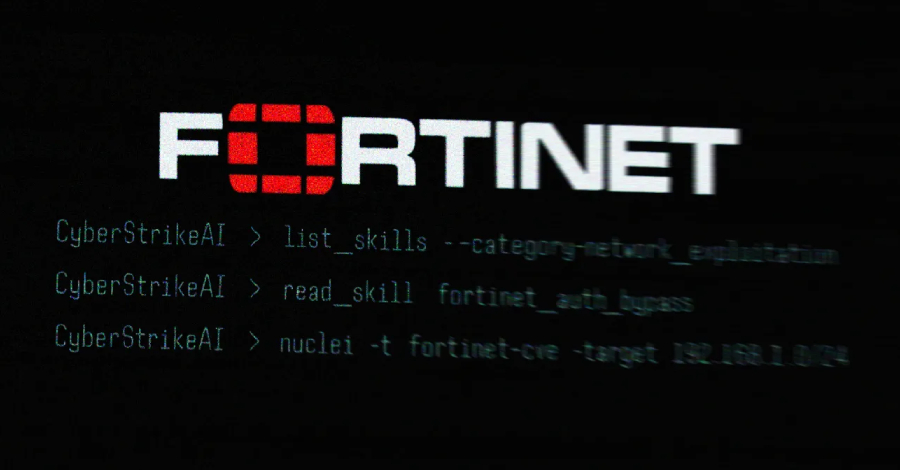
Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries
Ravie LakshmananMar 03, 2026Vulnerability / Artificial Intelligence The threat actor behind the recently disclosed artificial intelligence (AI)-assisted campaign targeting Fortinet […]
LLMs can unmask pseudonymous users at scale with surprising accuracy
Recall at various precision thresholds. Recall at various precision thresholds. In a third experiment, the researchers took 5,000 users from […]
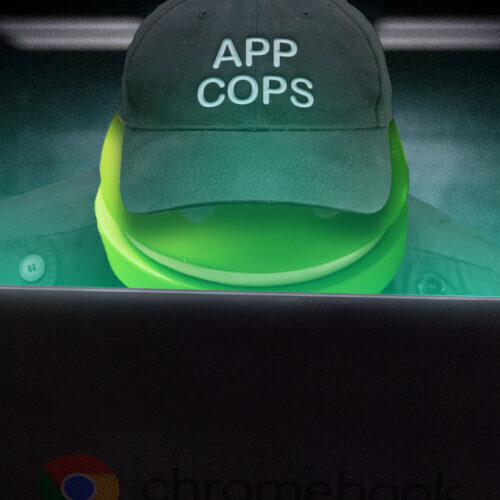
With developer verification, Google’s Apple envy threatens to dismantle Android’s open legacy
Skip to content Google’s very own walled garden Questions remain as Google prepares to lock down Android app distribution in […]
AI Agents: The Next Wave Identity Dark Matter – Powerful, Invisible, and Unmanaged
The Rise of MCPs in the Enterprise The Model Context Protocol (MCP) is quickly becoming a practical way to push […]
Starkiller Phishing Suite Uses AitM Reverse Proxy to Bypass Multi-Factor Authentication
Cybersecurity researchers have disclosed details of a new phishing suite called Starkiller that proxies legitimate login pages to bypass multi-factor […]