Jan 13, 2025The Hacker NewsThreat Detection / Network Security In 2024, ransomware attacks targeting VMware ESXi servers reached alarming levels, […]
Category: Security
WordPress Skimmers Evade Detection by Injecting Themselves into Database Tables
Cybersecurity researchers are warning of a new stealthy credit card skimmer campaign that targets WordPress e-commerce checkout pages by inserting […]
Expired Domains Allowed Control Over 4,000 Backdoors on Compromised Systems
Jan 13, 2025Ravie LakshmananMalware / Domain Security No less than 4,000 unique web backdoors previously deployed by various threat actors […]
Microsoft will forcibly install the new Outlook app on Windows 10 in February
While making much of the end of support for Windows 10, practically begging users to move on to Windows 11, […]
Microsoft Sues Hacking Group Exploiting Azure AI for Harmful Content Creation
Jan 11, 2025Ravie LakshmananAI Security / Cybersecurity Microsoft has revealed that it’s pursuing legal action against a “foreign-based threat–actor group” […]
DoJ Indicts Three Russians for Operating Crypto Mixers Used in Cybercrime Laundering
Jan 11, 2025Ravie LakshmananFinancial Crime / Cryptocurrency The U.S. Department of Justice (DoJ) on Friday indicted three Russian nationals for […]
Microsoft sues service for creating illicit content with its AI platform
Microsoft and others forbid using their generative AI systems to create various content. Content that is off limits includes materials […]
Taking the Pain Out of Cybersecurity Reporting: A Practical Guide for MSPs
Cybersecurity reporting is a critical yet often overlooked opportunity for service providers managing cybersecurity for their clients, and specifically for […]
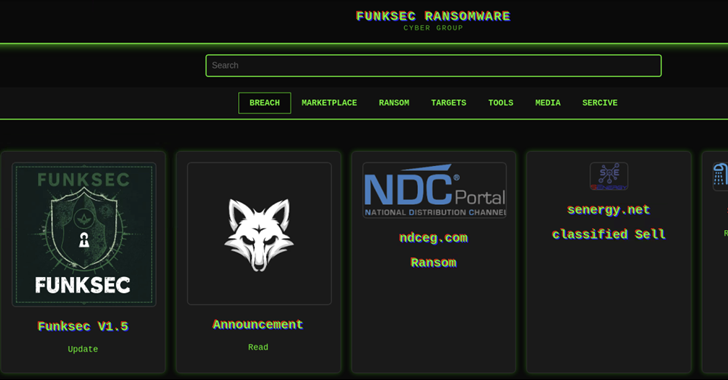
AI-Driven Ransomware FunkSec Targets 85 Victims Using Double Extortion Tactics
Jan 10, 2025Ravie LakshmananArtificial Intelligence / Cybercrime Cybersecurity researchers have shed light on a nascent artificial intelligence (AI) assisted ransomware […]
Hands-On Walkthrough: Microsegmentation For all Users, Workloads and Devices by Elisity
Network segmentation remains a critical security requirement, yet organizations struggle with traditional approaches that demand extensive hardware investments, complex policy […]