Dec 17, 2024Ravie LakshmananCyber Espionage / Malware A suspected South Asian cyber espionage threat group known as Bitter targeted a […]
Category: Security
5 Practical Techniques for Effective Cyber Threat Hunting
Addressing cyber threats before they have a chance to strike or inflict serious damage is by far the best security […]
Experts call for proactivity to combat state-sponsored cyber threats in 2025
In 2024, opposing nation-states have utilized cyberattacks to project power and disruption from within their own borders. This shift has […]
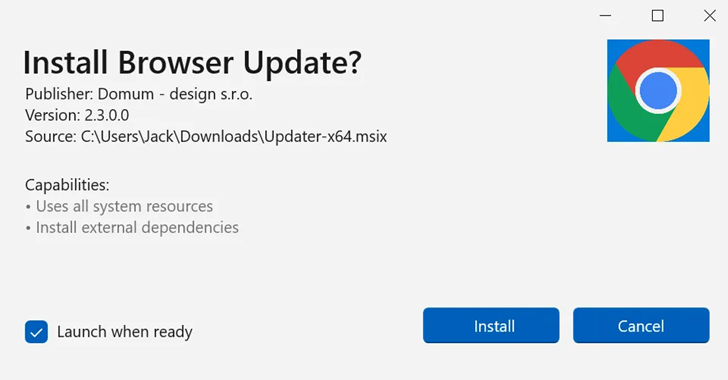
Hackers Exploit Webview2 to Deploy CoinLurker Malware and Evade Security Detection
Bogus software update lures are being used by threat actors to deliver a new stealer malware called CoinLurker. “Written in […]
The Mask APT Resurfaces with Sophisticated Multi-Platform Malware Arsenal
Dec 17, 2024Ravie LakshmananCyber Espionage / Mobile Security A little-known cyber espionage actor known as The Mask has been linked […]
CISA and FBI Raise Alerts on Exploited Flaws and Expanding HiatusRAT Campaign
Dec 17, 2024Ravie LakshmananNetwork Security / IoT Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added two […]
Hackers seek ransom after getting SSNs, banking info from state gov’t portal
Hackers trying to extort the Rhode Island government infiltrated the state’s public benefits system, causing state officials to shut down […]
2025 cybersecurity forecast: Preparing for the next generation of threats
As we navigate an increasingly digital landscape, the threats posed by cybercriminals are evolving at an alarming pace. The latest […]
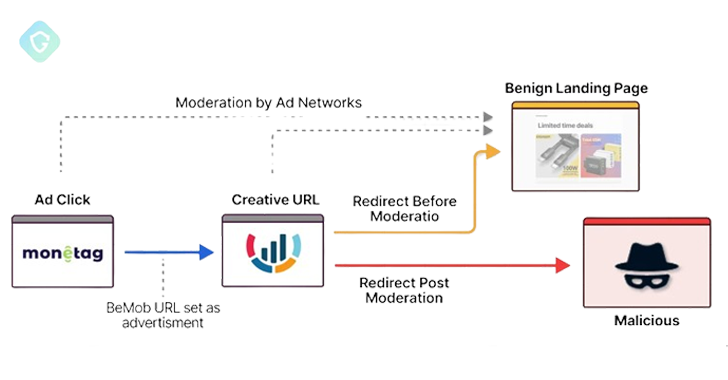
DeceptionAds Delivers 1M+ Daily Impressions via 3,000 Sites, Fake CAPTCHA Pages
Dec 16, 2024Ravie LakshmananMalvertising / Threat Intelligence Cybersecurity researchers have shed light on a previously undocumented aspect associated with ClickFix-style […]
NoviSpy Spyware Installed on Journalist’s Phone After Unlocking It With Cellebrite Tool
A Serbian journalist had his phone first unlocked by a Cellebrite tool and subsequently compromised by a previously undocumented spyware […]