Ravie LakshmananFeb 05, 2026Malware / Cyber Espionage The elusive Iranian threat group known as Infy (aka Prince of Persia) has […]
Category: Hackers
Hackers Exploit React2Shell to Hijack Web Traffic via Compromised NGINX Servers
Ravie LakshmananFeb 05, 2026Web Security / Vulnerability Cybersecurity researchers have disclosed details of an active web traffic hijacking campaign that […]
Hackers Exploit Metro4Shell RCE Flaw in React Native CLI npm Package
Ravie LakshmananFeb 03, 2026Open Source / Vulnerability Threat actors have been observed exploiting a critical security flaw impacting the Metro […]
82 percent of hackers now use AI
A future of cybersecurity, powered by AI, promises a world where it’s not just about defending against threats, but preemptively […]
Hackers Use LinkedIn Messages to Spread RAT Malware Through DLL Sideloading
Ravie LakshmananJan 20, 2026Malware / Threat Intelligence Cybersecurity researchers have uncovered a new phishing campaign that exploits social media private […]
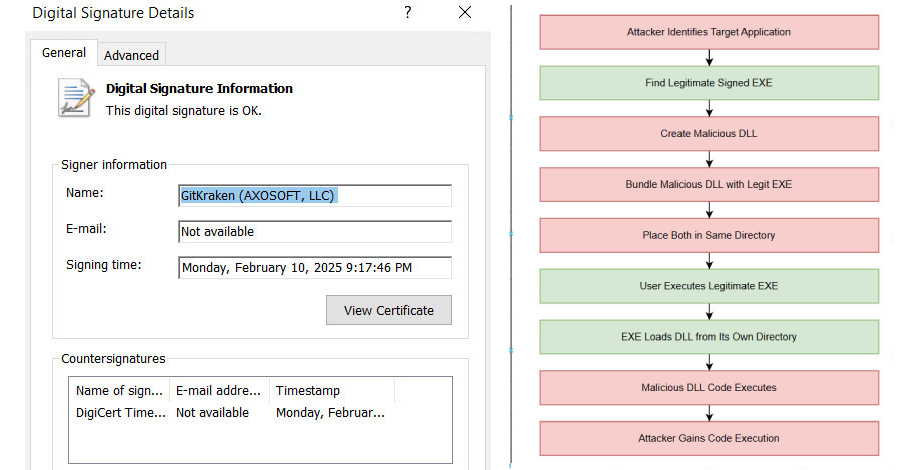
Hackers Exploit c-ares DLL Side-Loading to Bypass Security and Deploy Malware
Security experts have disclosed details of an active malware campaign that’s exploiting a DLL side-loading vulnerability in a legitimate binary […]
Hackers Hijack Blender 3D Assets to Deploy StealC V2 Data-Stealing Malware
Nov 25, 2025Ravie LakshmananMalware / Browser Security Cybersecurity researchers have disclosed details of a new campaign that has leveraged Blender […]
Hackers Weaponize Windows Hyper-V to Hide Linux VM and Evade EDR Detection
Nov 06, 2025Ravie LakshmananMalware / Network Security The threat actor known as Curly COMrades has been observed exploiting virtualization technologies […]
Hackers Used Snappybee Malware and Citrix Flaw to Breach European Telecom Network
Oct 21, 2025Ravie LakshmananCyber Espionage / Network Security A European telecommunications organization is said to have been targeted by a […]
Hackers Abuse Blockchain Smart Contracts to Spread Malware via Infected WordPress Sites
A financially motivated threat actor codenamed UNC5142 has been observed abusing blockchain smart contracts as a way to facilitate the […]