Ravie LakshmananApr 13, 2026Cybercrime / Threat Intelligence The U.S. Federal Bureau of Investigation (FBI), in partnership with the Indonesian National […]
Category: Security
⚡ Weekly Recap: Fiber Optic Spying, Windows Rootkit, AI Vulnerability Hunting and More
Ravie LakshmananApr 13, 2026Cybersecurity / Hacking Monday is back, and the weekend’s backlog of chaos is officially hitting the fan. We are […]
Your MTTD Looks Great. Your Post-Alert Gap Doesn’t
Anthropic restricted its Mythos Preview model last week after it autonomously found and exploited zero-day vulnerabilities in every major operating […]
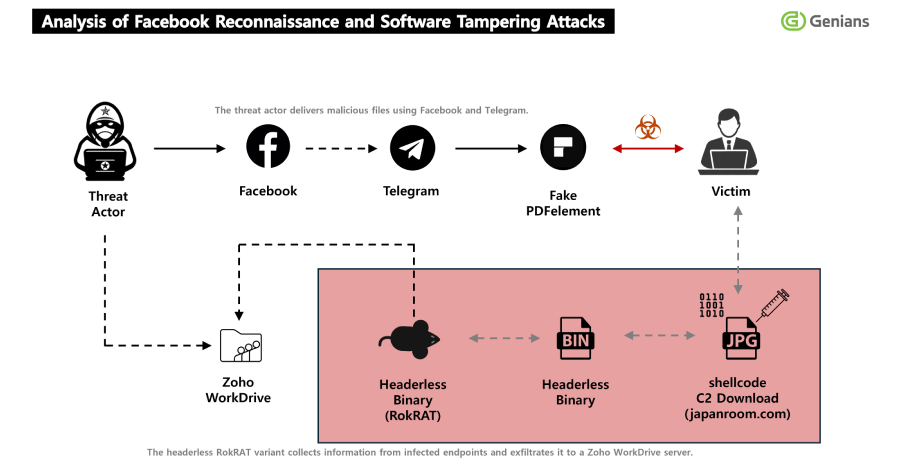
North Korea’s APT37 Uses Facebook Social Engineering to Deliver RokRAT Malware
Ravie LakshmananApr 13, 2026Social Engineering / Threat Intelligence The North Korean hacking group tracked as APT37 (aka ScarCruft) has been attributed […]
OpenAI Revokes macOS App Certificate After Malicious Axios Supply Chain Incident
OpenAI revealed a GitHub Actions workflow used to sign its macOS apps led to the download of the malicious Axios […]
CPUID Breach Distributes STX RAT via Trojanized CPU-Z and HWMonitor Downloads
Ravie LakshmananApr 12, 2026Malware / Threat Intelligence Unknown threat actors compromised CPUID (“cpuid[.]com”), a website that hosts popular hardware monitoring tools […]
Adobe Patches Actively Exploited Acrobat Reader Flaw CVE-2026-34621
Ravie LakshmananApr 12, 2026Vulnerability / Endpoint Security Adobe has released emergency updates to fix a critical security flaw in Acrobat […]
Citizen Lab: Law Enforcement Used Webloc to Track 500 Million Devices via Ad Data
Hungarian domestic intelligence, the national police in El Salvador, and several U.S. law enforcement and police departments have been attributed to […]
GlassWorm Campaign Uses Zig Dropper to Infect Multiple Developer IDEs
Ravie LakshmananApr 10, 2026Malware / Blockchain Cybersecurity researchers have flagged yet another evolution of the ongoing GlassWorm campaign, which employs a […]
Browser Extensions Are the New AI Consumption Channel That No One Is Talking About
While much of the discussion on AI security centers around protecting ‘shadow’ AI and GenAI consumption, there’s a wide-open window nobody’s guarding: AI […]