The U.S. Department of Justice (DoJ) on Thursday announced the disruption of command-and-control (C2) infrastructure used by several Internet of […]
Category: Security
Apple Warns Older iPhones Vulnerable to Coruna, DarkSword Exploit Kit Attacks
Ravie LakshmananMar 20, 2026Mobile Security / Malware Apple is urging users who are still running an outdated version of iOS […]
Millions of iPhones can be hacked with a new tool found in the wild
DarkSword, a powerful iPhone-hacking technique, has been discovered in use by Russian hackers. iPhone hacking techniques have sometimes been described almost […]
Speagle Malware Hijacks Cobra DocGuard to Steal Data via Compromised Servers
Ravie LakshmananMar 19, 2026Cyber Espionage / Threat Intelligence Cybersecurity researchers have flagged a new malware dubbed Speagle that hijacks the […]
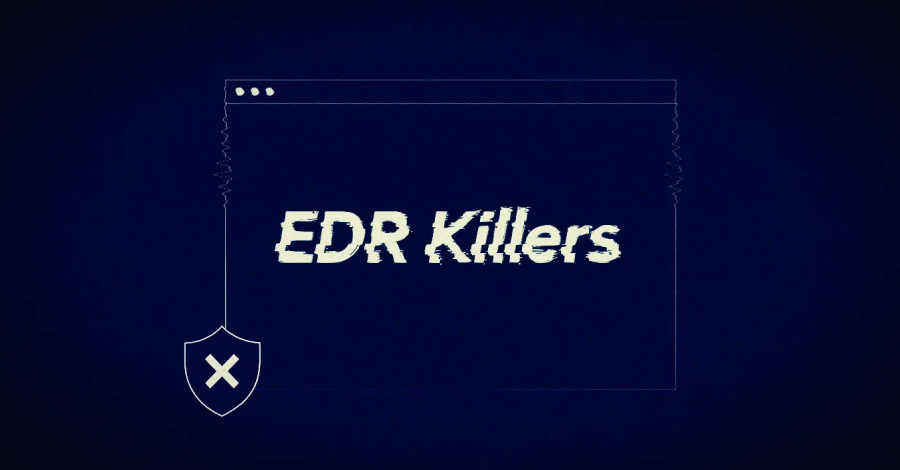
54 EDR Killers Use BYOVD to Exploit 34 Signed Vulnerable Drivers and Disable Security
A new analysis of endpoint detection and response (EDR) killers has revealed that 54 of them leverage a technique known […]
Google details new 24-hour process to sideload unverified Android apps
The “advanced flow” will be available before verification enforcement begins later this year. Google is planning big changes for Android […]
ThreatsDay Bulletin: FortiGate RaaS, Citrix Exploits, MCP Abuse, LiveChat Phish & More
ThreatsDay Bulletin is back on The Hacker News, and this week feels off in a familiar way. Nothing loud, nothing […]
New Perseus Android Banking Malware Monitors Notes Apps to Extract Sensitive Data
Ravie LakshmananMar 19, 2026Malware / Mobile Security Cybersecurity researchers have disclosed a new Android malware family called Perseus that’s being […]
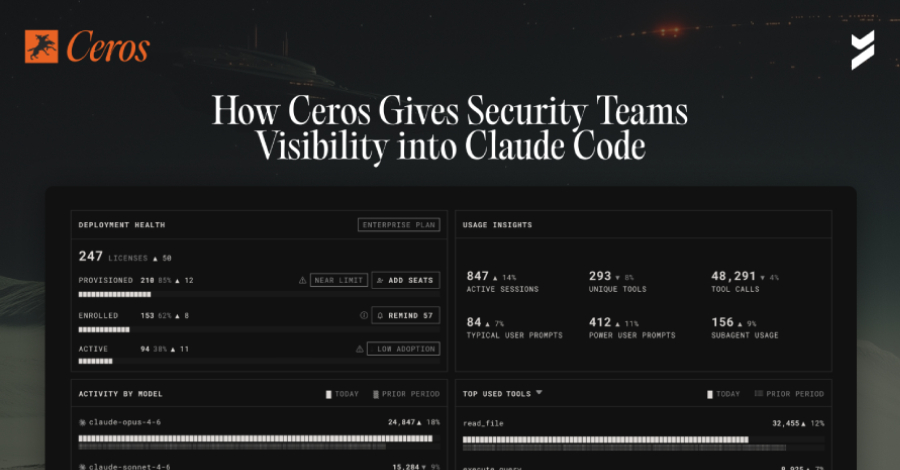
How Ceros Gives Security Teams Visibility and Control in Claude Code
Security teams have spent years building identity and access controls for human users and service accounts. But a new category […]
DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for Full Device Takeover
A new exploit kit for Apple iOS devices designed to steal sensitive data from is being wielded by multiple threat […]