While passwords remain the first line of defense for protecting user accounts against unauthorized access, the methods for creating strong […]
Category: Hackers
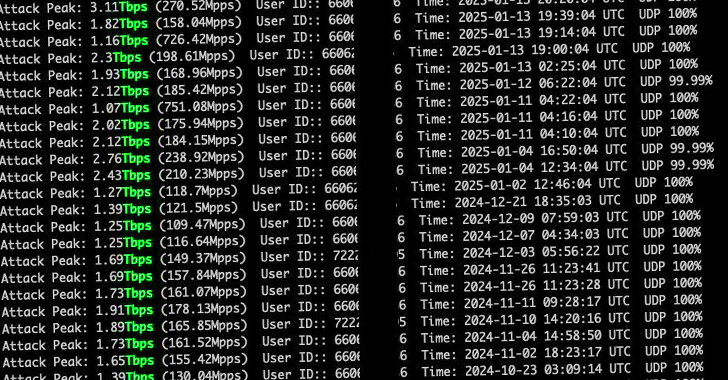
Hackers Exploit Zero-Day in cnPilot Routers to Deploy AIRASHI DDoS Botnet
Threat actors are exploiting an unspecified zero-day vulnerability in Cambium Networks cnPilot routers to deploy a variant of the AISURU […]
Hackers Deploy Malicious npm Packages to Steal Solana Wallet Keys via Gmail SMTP
Jan 20, 2025Ravie LakshmananSupply Chain Attack / Solana Cybersecurity researchers have identified three sets of malicious packages across the npm […]
Hackers Hide Malware in Images to Deploy VIP Keylogger and 0bj3ctivity Stealer
Jan 16, 2025Ravie LakshmananMalware / Ransomware Threat actors have been observed concealing malicious code in images to deliver malware such […]
Hackers Exploit Aviatrix Controller Vulnerability to Deploy Backdoors and Crypto Miners
Jan 13, 2025Ravie LakshmananVulnerability / Cloud Security A recently disclosed critical security flaw impacting the Aviatrix Controller cloud networking platform […]
Hackers Exploiting Critical Fortinet EMS Vulnerability to Deploy Remote Access Tools
Dec 20, 2024Ravie LakshmananVulnerability / Cyber Attack A now-patched critical security flaw impacting Fortinet FortiClient EMS is being exploited by […]
APT29 Hackers Target High-Value Victims Using Rogue RDP Servers and PyRDP
Dec 18, 2024Ravie LakshmananCyber Espionage / Malware The Russia-linked APT29 threat actor has been observed repurposing a legitimate red teaming […]
Hackers Use Microsoft MSC Files to Deploy Obfuscated Backdoor in Pakistan Attacks
Dec 17, 2024Ravie LakshmananCyber Attack / Malware A new phishing campaign has been observed employing tax-themed lures to deliver a […]
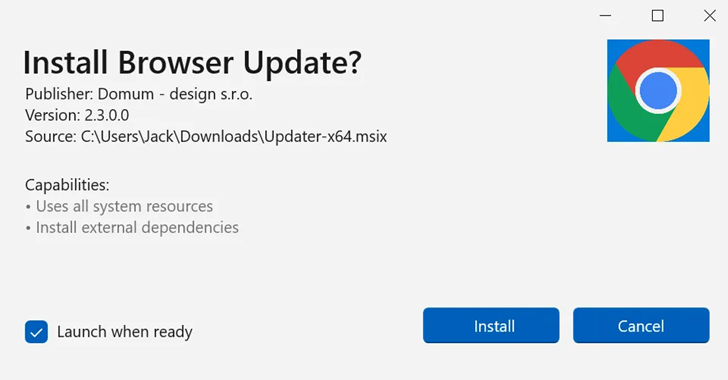
Hackers Exploit Webview2 to Deploy CoinLurker Malware and Evade Security Detection
Bogus software update lures are being used by threat actors to deliver a new stealer malware called CoinLurker. “Written in […]