Every CISO knows the uncomfortable truth about their Security Operations Center: the people most responsible for catching threats in real time are the people with the least experience. Tier 1 analysts sit at the front line of detection, and yet they are also the most vulnerable to the cognitive and organizational pressures that quietly erode SOC performance over time.
The Paradox at the Gate: Why Tier 1 Carries the Weight but Lacks the Armor
Tier 1 is the layer that processes the highest volume of alerts, performs initial triage, and determines what gets escalated. But it is built on a foundation that is structurally fragile. Entry-level analysts, high turnover rates, and relentless alert queues create conditions where even well-designed detection rules fail to translate into timely, accurate responses.
The paradox is here:
- Tier 1 performance defines SOC performance;
- But Tier 1 is often the least supported, least empowered, and most cognitively overloaded layer
Tier 1 analysts face a daily avalanche of alerts. Over time, this leads to:
- Alert fatigue: constant exposure to high volumes reduces sensitivity to real danger.
- Decision fatigue: repeated micro-decisions degrade judgment quality.
- Cognitive overload: too many dashboards, too little context.
- False-positive conditioning: when 90% of alerts are benign, skepticism becomes automatic.
- Burnout and turnover: institutional memory evaporates
For CISOs, these are not HR problems. It’s a business risk. When Tier 1 hesitates, misses, or delays escalation:
- Dwell time increases,
- Incident costs rise,
- Detection quality degrades,
- Executive confidence in security drops.
If Tier 1 is weak, the entire SOC becomes reactive rather than predictive.
The Core Engine Room: Monitoring and Triage as Business-Critical Workflows
Tier 1 owns two foundational SOC processes: monitoring and alert triage. Monitoring is the continuous process of ingesting signals from across the environment — endpoints, networks, cloud infrastructure, identity systems — and applying detection logic to surface events of potential concern.
Triage is what happens next: the structured, human-driven process of evaluating those events, assigning severity, ruling out false positives, and determining whether escalation is warranted.
Basically, these are routine tasks. Watch telemetry. Sort alerts into true positive/false positive/needs escalation. But these also are revenue protection mechanisms since they determine MTTR, MTTD, and resource allocation efficiency. When these workflows are inefficient:
- Tier 2 and Tier 3 drown in noise,
- Incident response begins late,
- Business disruption expands,
- Operational costs increase,
- Regulatory exposure grows.
Intelligence as Oxygen: The Foundation of Tier 1 Effectiveness
Tier 1 cannot operate effectively in a vacuum, and raw alerts without context are just digital shadows. Actionable threat intelligence turns data into decisions. For a Tier 1 analyst asking, “Is this connected to an active campaign targeting our sector?”, it provides:
- IOC validation,
- Campaign context,
- TTP mapping,
- Infrastructure associations,
- Malware family attribution.
Tier 1 analysts need threat intelligence more urgently than anyone else in the SOC, precisely because they make the most time-sensitive decisions with the least contextual background.
Integrate actionable feeds and lookup enrichment into your SOC workflows to speed detection and improve operational resilience
Step 1: Detect What Others Miss. Powering Monitoring with Live Threat Intelligence Feeds
The first step toward a high-impact Tier 1 is upgrading the intelligence foundation of monitoring itself. Most SOC environments rely on detection rules built from static signatures or behavioral heuristics — logic that was accurate when written but degrades as adversaries adapt.
Actionable threat intelligence feeds continuously inject fresh, verified indicators of compromise directly into the detection infrastructure. Rather than flagging anomalies and waiting for an analyst to research them, a feed-enriched monitoring layer flags activity that has already been confirmed as malicious through real-world analysis. Detections become based on behavioral ground truth, not statistical deviation.
The operational effect on early detection is substantial. It compresses the window of exposure and dramatically reduces the cost of eventual containment.
ANY.RUN’s Threat Intelligence Feeds aggregate indicators (malicious IPs, URLs, domains) drawn from a continuously operating malware analysis sandbox that processes real-world threats in real time. This means the data reflects active threat activity observed through dynamic execution analysis, not historical reporting or third-party aggregation alone. Adversaries who modify their malware to evade static signatures cannot easily evade behavioral observation.
 |
| TI Feeds: data, benefits, integrations |
Delivered in STIX and MISP formats, TI Feeds integrate directly with SIEMs, firewalls, DNS resolvers, and endpoint detection systems. Each indicator carries contextual metadata like malware families and behavioral tags, so that a detection is not just a flag but an explanation.
For the business, intelligence-powered monitoring reduces MTTD, improves detection precision, and generates a measurable return on the broader security stack investment by ensuring that what gets detected is what actually matters.
Step 2: From Flag to Finding. Enriching Every Alert with the Context Analysts Actually Need
Before an analyst can enrich an alert, they often face a more immediate problem: a suspicious file or link has surfaced, and its nature is genuinely unknown. This is where the ANY.RUN Interactive Sandbox becomes a direct triage asset.
Rather than relying on static reputation checks alone, analysts can submit the artifact to the sandbox and observe its actual behavior in a live execution environment — watching in real time as the file makes network connections, modifies the registry, drops additional payloads, or attempts to evade detection. Within minutes, the sandbox produces a verdict grounded in what the sample actually does, not just what it looks like.
View sandbox analysis of a suspicious .exe file
 |
| Sandbox detonation detects ScreenConnect malware |
But detection is only the beginning of a T1 analyst’s job. Once an alert surfaces, the analyst must determine whether it represents a genuine threat, understand what it means, and decide what to do with it — all under time pressure and against a queue of competing alerts. Without enrichment, this determination relies on analyst experience and manual research, both of which are in short supply at Tier 1.
The quality and speed of enrichment determine the quality and speed of triage. Deep enrichment, grounded in behavioral analysis, allows analysts to reason about the actual risk of a detection rather than guessing at it.
ANY.RUN’s Threat Intelligence Lookup delivers this depth on demand. Analysts can query any indicator — domain, IP, file hash, URL — and receive immediate context drawn from the sandbox’s analysis repository: full behavioral reports showing how the artifact executed, associated malware families and threat categories, network indicators observed during analysis, and connections to broader malicious infrastructure. A lookup is fast enough to fit into the triage workflow rather than interrupting it.
domainName:”priutt-title.com”
 |
| TI Lookup domain search with “Malicious” verdict and additional IOCs |
A single lookup allows us to understand that a doubtful domain spotted in the network traffic is most probably malicious, engaged in campaigns targeting IT, finance, and educational businesses all over the world right now, and linked to more indicators that can be used for further detection tuning.
This changes how T1 operates across several dimensions:
- Analysts make faster, more confident decisions because they have evidence rather than inference.
- Escalation notes improve because analysts can articulate what they found and why it matters, reducing back-and-forth with Tier 2 and accelerating the handoff.
- False positives are closed with greater certainty, improving the precision of the escalation pipeline.
For business objectives, enriched triage supports several priorities simultaneously:
- It accelerates MTTD and MTTR, which are key metrics for both security program effectiveness and regulatory compliance.
- It improves the quality of incident documentation for post-incident review, insurance claims, and regulatory reporting.
- It reduces analyst burnout by replacing frustrating ambiguity with actionable clarity.
- Finally, it ensures that the SOC’s output reflects genuine analysis rather than overwhelmed guesswork.
Step 3: Security That Compounds. Integrating ANY.RUN into Your Existing Stack
Individual capabilities — however strong — deliver limited value when they operate in isolation. The third and most strategically significant step is integration: connecting ANY.RUN’s Threat Intelligence Feeds, Lookup, and Sandbox into the existing security infrastructure so that intelligence flows automatically across every layer of the environment.
This is where investment in T1 intelligence capabilities translates into organization-wide risk reduction.
- SIEMs that ingest TI Feeds generate higher-precision alerts, because the detection layer is operating from verified behavioral indicators rather than generic rules.
- Firewalls and DNS resolvers that consume the same feeds block malicious infrastructure at the perimeter, reducing the volume of threats that reach endpoints and analysts in the first place.
- EDR systems enriched with sandbox-derived behavioral signatures detect malware that evades signature-based approaches.
- The entire stack becomes more coherent because it shares a common intelligence foundation.
ANY.RUN supports this integration architecture through standard formats and APIs designed for compatibility with the security products already in deployment. STIX and MISP feed delivery integrates with leading SIEM and SOAR solutions. The TI Lookup API enables direct enrichment from within analyst workflows(ticketing systems, investigation dashboards, custom scripts) without requiring analysts to leave their primary interface. The sandbox itself can receive samples programmatically, enabling automated analysis pipelines that feed results back into detection and response systems.
 |
| ANY.RUN integration capabilities |
For T1 teams, the day-to-day effect of integration is a reduction in the manual effort that currently consumes analyst time. Indicators enriched automatically before triage, feeds that update detection logic without human intervention, escalation data that populates from sandbox analysis rather than manual documentation — these changes shift analyst effort from information gathering to genuine investigation. T1 becomes faster without becoming larger.
For CISOs, the business case for integration centers on compounding returns. Each point of integration multiplies the value of the intelligence investment: a feed consumed by five security controls delivers five times the coverage of a feed consumed by one.
This coherence also strengthens the organization’s posture in conversations with the board, insurers, and regulators. An integrated, intelligence-driven security architecture demonstrates not just that controls exist, but that they are actively informed by current threat activity, a substantively different claim than checkbox compliance.
Integrate dynamic malware analysis, fresh intelligence feeds, and contextual search to improve detection quality and business outcomes
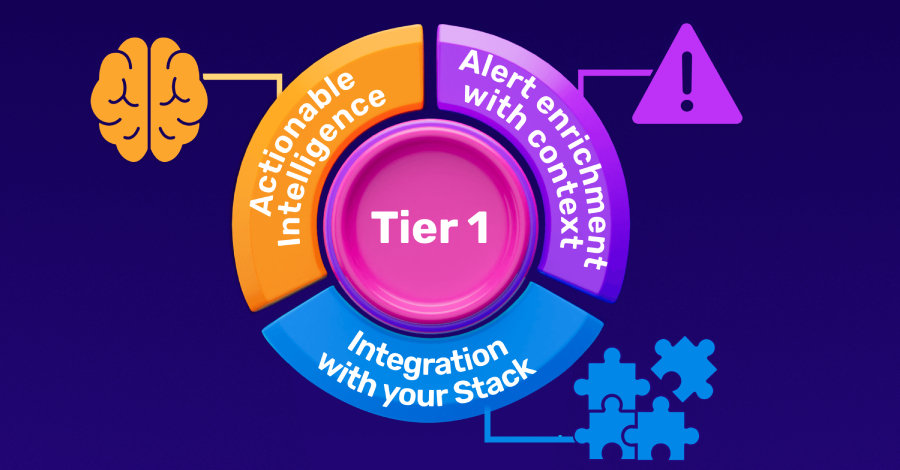
Three Steps, One Outcome: A Tier 1 That Actually Protects the Business
The path to a high-impact Tier 1 is not hiring more analysts or writing more detection rules. It lies in addressing the structural shortcomings that make T1 fragile: monitoring that cannot reflect current threats, triage that lacks the context to be decisive, and intelligence capabilities that remain disconnected from the stack they should be informing.
ANY.RUN’s Threat Intelligence Feeds, Lookup, and Interactive Sandbox form a closed loop — from behavioral analysis to detection to investigation — that addresses each of the steps to top performance without adding operational complexity. The Sandbox generates ground truth. The Feeds operationalize it across the detection layer. The Lookup makes the same analytical depth available on demand for every analyst, regardless of experience.
CISOs who prioritize this investment are not just improving SOC metrics. They are changing the equation for every threat actor who targets their organization. A Tier 1 team that detects early, triages with confidence, and escalates accurately is one of the highest-leverage risk reduction assets a security program can build.
Combine live TI Feeds with indicator enrichment to transform monitoring into high-confidence detection.
Found this article interesting? This article is a contributed piece from one of our valued partners. Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.