In an unexpected yet exciting move, Google has released the source code for the Pebble smartwatch operating system on GitHub. […]
Author: Admin
OpenAI’s Sam Altman calls DeepSeek ‘impressive’ but promises to launch ‘much better models’ soon
(Image credit: Future) OpenAI’s Sam Altman called DeepSeek’s viral AI model “impressive” In response, he says, “we will obviously deliver […]
AMD’s Ryzen 9 9950X3D CPU could be on sale soon – but I’m still worried about the price
Image Credit: AMD ASRock has listed the unreleased Ryzen 9 X3D CPUs on its website The Ryzen 9 9950X3D and […]
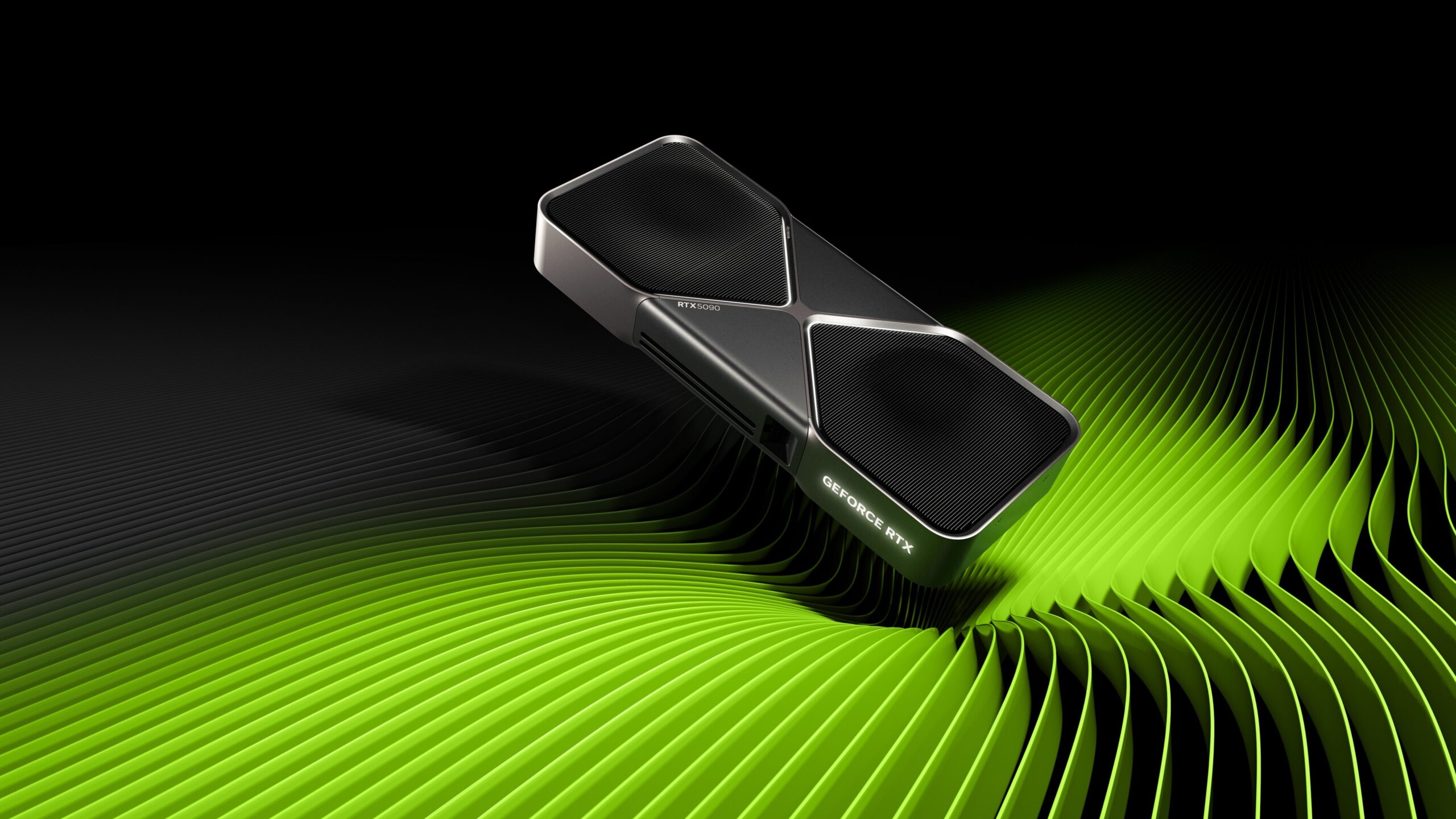
Scalpers are salivating right now – MSI suggests RTX 5090 supply will be tight due to Nvidia’s shortage
(Image credit: Nvidia) MSI says there will be a limited supply of the RTX 5090 at launch This shortage reportedly […]
AI SOC Analysts: Propelling SecOps into the future
Triaging and investigating alerts is central to security operations. As SOC teams strive to keep up with ever-increasing alert volumes […]
Ransomware Targets ESXi Systems via Stealthy SSH Tunnels for C2 Operations
Jan 28, 2025Ravie LakshmananRansomware / Threat Intelligence Cybersecurity researchers have found that ransomware attacks targeting ESXi systems are also leveraging […]
Amazon has some of the best MacBook Air deals I’ve seen since Black Friday
(Image credit: Future) I love my Apple MacBook and wouldn’t choose any other laptop to work on. I have the […]
Are Nvidia’s RTX 5060 GPUs about to arrive? Rumor hints they might be – with the RTX 5060 Ti potentially coming with 16GB VRAM
(Image credit: Future / John Loeffler) Maxsun has filed RTX 5060 models with the Eurasian Economic Commission Those filings could […]
Google Maps will honor President Trump’s renaming of the Gulf of Mexico to the Gulf of America and Denali to Mount McKinley
One of Donald Trump’s first pledges after being sworn in as the 47th president of the USA was to rename […]
How Long Does It Take Hackers to Crack Modern Hashing Algorithms?
While passwords remain the first line of defense for protecting user accounts against unauthorized access, the methods for creating strong […]