Fears of a data breach dominate consumer concerns, with 64 percent naming breaches as their top privacy worry. A new […]
Author: Admin
OAuth Redirect Flaw in Airline Travel Integration Exposes Millions to Account Hijacking
Jan 28, 2025Ravie Lakshmanan Cybersecurity researchers have disclosed details of a now-patched account takeover vulnerability affecting a popular online travel […]
Don’t get too attached to DeepSeek – it’ll never survive in the US
(Image credit: Getty Images) Has everyone lost their collective minds? How did DeepSeek go from a relatively unknown Chinese startup […]
DeepSeek has already dethroned ChatGPT – is it coming for Midjourney and DALL-E next?
(Image credit: Adobe Stock) DeepSeek has released a new family of multimodal LLMs The new Janus-Pro family is available for […]
Google gives Pebble smartwatches a second life with GitHub source code release
In an unexpected yet exciting move, Google has released the source code for the Pebble smartwatch operating system on GitHub. […]
OpenAI’s Sam Altman calls DeepSeek ‘impressive’ but promises to launch ‘much better models’ soon
(Image credit: Future) OpenAI’s Sam Altman called DeepSeek’s viral AI model “impressive” In response, he says, “we will obviously deliver […]
AMD’s Ryzen 9 9950X3D CPU could be on sale soon – but I’m still worried about the price
Image Credit: AMD ASRock has listed the unreleased Ryzen 9 X3D CPUs on its website The Ryzen 9 9950X3D and […]
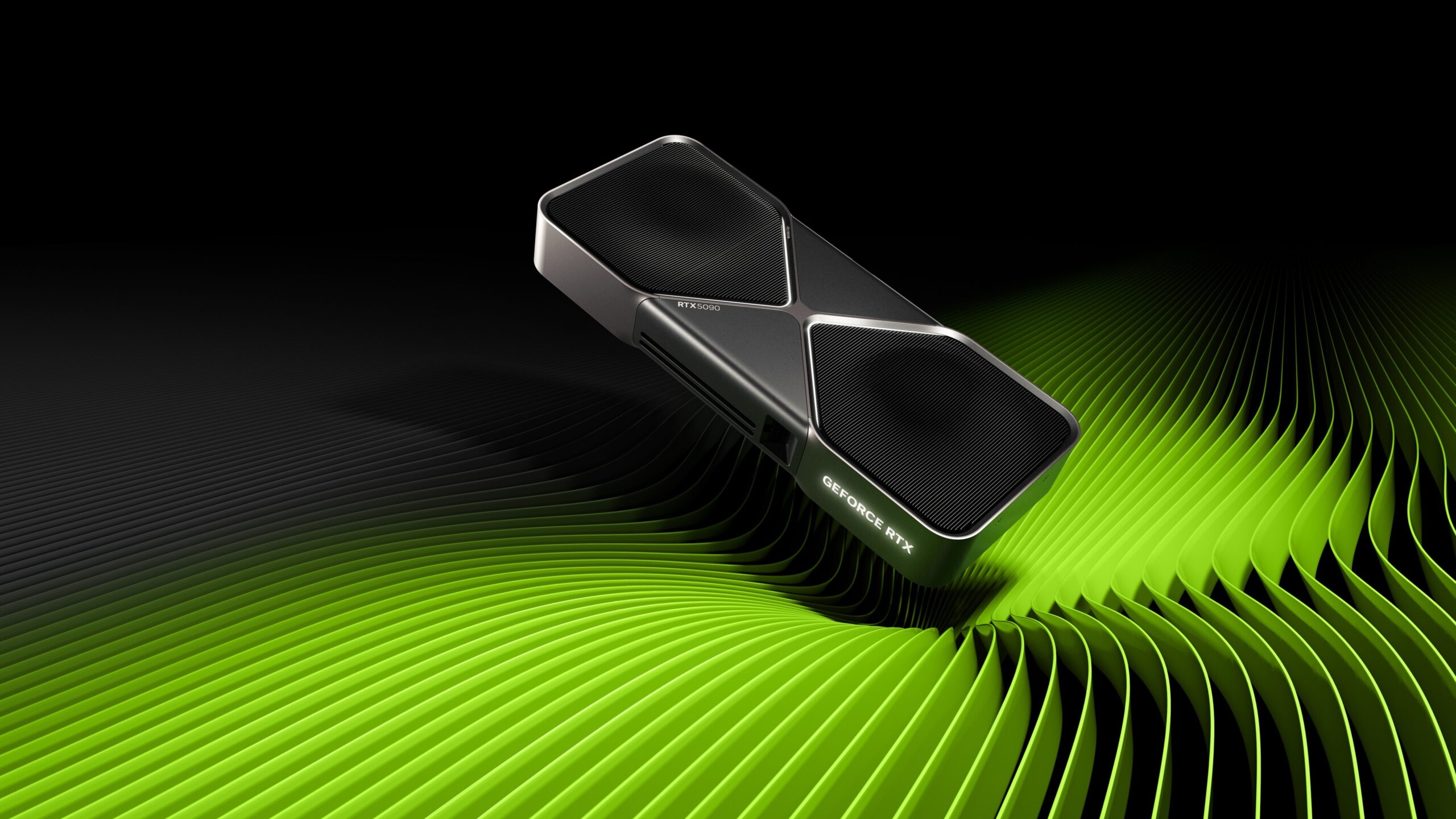
Scalpers are salivating right now – MSI suggests RTX 5090 supply will be tight due to Nvidia’s shortage
(Image credit: Nvidia) MSI says there will be a limited supply of the RTX 5090 at launch This shortage reportedly […]
AI SOC Analysts: Propelling SecOps into the future
Triaging and investigating alerts is central to security operations. As SOC teams strive to keep up with ever-increasing alert volumes […]
Ransomware Targets ESXi Systems via Stealthy SSH Tunnels for C2 Operations
Jan 28, 2025Ravie LakshmananRansomware / Threat Intelligence Cybersecurity researchers have found that ransomware attacks targeting ESXi systems are also leveraging […]